VIRTUAL MACHINE MANAGEMENT GUIDE
Managing Virtual Machines in Red Hat Virtualization
Abstract
Chapter 1. Introduction
1.1. Audience
1.2. Supported Virtual Machine Operating Systems
Table 1.1. Operating systems that can be used as guest operating systems
| Operating System | Architecture |
|---|---|
Red Hat Enterprise Linux 3 | 32-bit, 64-bit |
Red Hat Enterprise Linux 4 | 32-bit, 64-bit |
Red Hat Enterprise Linux 5 | 32-bit, 64-bit |
Red Hat Enterprise Linux 6 | 32-bit, 64-bit |
Red Hat Enterprise Linux 7 | 64-bit |
Red Hat Enterprise Linux Atomic Host 7 | 64-bit |
SUSE Linux Enterprise Server 10 (select for the guest type in the user interface) | 32-bit, 64-bit |
SUSE Linux Enterprise Server 11 (SPICE drivers (QXL) are not supplied by Red Hat. However, the distribution's vendor may provide SPICE drivers as part of their distribution.) | 32-bit, 64-bit |
Ubuntu 12.04 (Precise Pangolin LTS) | 32-bit, 64-bit |
Ubuntu 12.10 (Quantal Quetzal) | 32-bit, 64-bit |
Ubuntu 13.04 (Raring Ringtail) | 32-bit, 64-bit |
Ubuntu 13.10 (Saucy Salamander) | 32-bit, 64-bit |
Windows 7 | 32-bit, 64-bit |
Windows 8 | 32-bit, 64-bit |
Windows 8.1 | 32-bit, 64-bit |
Windows 10 | 32-bit, 64-bit |
Windows Server 2008 | 32-bit, 64-bit |
Windows Server 2008 R2 | 64-bit |
Windows Server 2012 | 64-bit |
Windows Server 2012 R2 | 64-bit |
Table 1.2. Guest operating systems that are supported by Global Support Services
| Operating System | Architecture | SPICE Support |
|---|---|---|
Red Hat Enterprise Linux 5 | 32-bit, 64-bit | No |
Red Hat Enterprise Linux 6 | 32-bit, 64-bit | Yes (on Red Hat Enterprise Linux 6.8 and above) |
Red Hat Enterprise Linux 7 | 64-bit | Yes (on Red Hat Enterprise Linux 7.2 and above) |
Red Hat Enterprise Linux Atomic Host 7 | 64-bit | Yes |
SUSE Linux Enterprise Server 10 (select for the guest type in the user interface) | 32-bit, 64-bit | No |
SUSE Linux Enterprise Server 11 (SPICE drivers (QXL) are not supplied by Red Hat. However, the distribution's vendor may provide SPICE drivers as part of their distribution.) | 32-bit, 64-bit | No |
Windows 7 | 32-bit, 64-bit | Yes |
Windows 8 | 32-bit, 64-bit | No |
Windows 8.1 | 32-bit, 64-bit | No |
Windows 10 | 32-bit, 64-bit | No |
Windows Server 2008 | 32-bit, 64-bit | No |
Windows Server 2008 R2 | 64-bit | No |
Windows Server 2012 | 64-bit | No |
Windows Server 2012 R2 | 64-bit | No |
Note
Note
1.3. Virtual Machine Performance Parameters
Table 1.3. Supported virtual machine parameters
| Parameter | Number | Note |
|---|---|---|
| Virtualized CPUs | 240 | Per virtual machine running on a Red Hat Enterprise Linux 6 host. |
| Virtualized CPUs | 240 | Per virtual machine running on a Red Hat Enterprise Linux 7 host. |
| Virtualized RAM | 4000 GB | For a 64 bit virtual machine. |
| Virtualized RAM | 4 GB | Per 32 bit virtual machine. Note, the virtual machine may not register the entire 4 GB. The amount of RAM that the virtual machine recognizes is limited by its operating system. |
| Virtualized storage devices | 8 | Per virtual machine. |
| Virtualized network interface controllers | 8 | Per virtual machine. |
| Virtualized PCI devices | 32 | Per virtual machine. |
1.4. Installing Supporting Components on Client Machines
1.4.1. Installing Console Components
1.4.1.1. Installing Remote Viewer on Red Hat Enterprise Linux
Procedure 1.1. Installing Remote Viewer on Linux
- Install the virt-viewer package:
# yum install virt-viewer
- Restart your browser for the changes to take effect.
1.4.1.2. Installing Remote Viewer on Windows
Procedure 1.2. Installing Remote Viewer on Windows
- Open a web browser and download one of the following installers according to the architecture of your system.
- Virt Viewer for 32-bit Windows:
https://your-manager-fqdn/ovirt-engine/services/files/spice/virt-viewer-x86.msi
- Virt Viewer for 64-bit Windows:
https://your-manager-fqdn/ovirt-engine/services/files/spice/virt-viewer-x64.msi
- Open the folder where the file was saved.
- Double-click the file.
- Click Run if prompted by a security warning.
- Click Yes if prompted by User Account Control.
1.4.2. Installing usbdk on Windows
Procedure 1.3. Installing usbdk on Windows
- Open a web browser and download one of the following installers according to the architecture of your system.
- usbdk for 32-bit Windows:
https://[your manager's address]/ovirt-engine/services/files/spice/usbdk-x86.msi
- usbdk for 64-bit Windows:
https://[your manager's address]/ovirt-engine/services/files/spice/usbdk-x64.msi
- Open the folder where the file was saved.
- Double-click the file.
- Click Run if prompted by a security warning.
- Click Yes if prompted by User Account Control.
Chapter 2. Installing Linux Virtual Machines
- Create a blank virtual machine on which to install an operating system.
- Add a virtual disk for storage.
- Add a network interface to connect the virtual machine to the network.
- Install an operating system on the virtual machine. See your operating system's documentation for instructions.
- Red Hat Enterprise Linux 6: https://access.redhat.com/documentation/en-US/Red_Hat_Enterprise_Linux/6/html/Installation_Guide/index.html
- Red Hat Enterprise Linux 7: https://access.redhat.com/documentation/en-US/Red_Hat_Enterprise_Linux/7/html/Installation_Guide/index.html
- Red Hat Enterprise Linux Atomic Host 7: https://access.redhat.com/documentation/en/red-hat-enterprise-linux-atomic-host/7/single/installation-and-configuration-guide/
- Register the virtual machine with the Content Delivery Network and subscribe to the relevant entitlements.
- Install guest agents and drivers for additional virtual machine functionality.
2.1. Creating a Linux Virtual Machine
Procedure 2.1. Creating Linux Virtual Machines
- Click the tab.
- Click the button to open the New Virtual Machine window.
- Select a Linux variant from the Operating System drop-down list.
- Enter a Name for the virtual machine.
- Add storage to the virtual machine. or a virtual disk under Instance Images.
- Click and select an existing virtual disk.
- Click and enter a Size(GB) and Alias for a new virtual disk. You can accept the default settings for all other fields, or change them if required. See Section A.3, “Explanation of Settings in the New Virtual Disk and Edit Virtual Disk Windows” for more details on the fields for all disk types.
- Click .
- Connect the virtual machine to the network. Add a network interface by selecting a vNIC profile from the nic1 drop-down list at the bottom of the General tab.
- Specify the virtual machine's Memory Size on the System tab.
- Choose the First Device that the virtual machine will boot from on the Boot Options tab.
- You can accept the default settings for all other fields, or change them if required. For more details on all fields in the New Virtual Machine window, see Section A.1, “Explanation of Settings in the New Virtual Machine and Edit Virtual Machine Windows”.
- Click .
Down. Before you can use this virtual machine, you must install an operating system and register with the Content Delivery Network.2.2. Starting the Virtual Machine
2.2.1. Starting a Virtual Machine
Procedure 2.2. Starting Virtual Machines
- Click the Virtual Machines tab and select a virtual machine with a status of
Down. - Click the run (
 ) button.Alternatively, right-click the virtual machine and select .
) button.Alternatively, right-click the virtual machine and select .
Up, and the operating system installation begins. Open a console to the virtual machine if one does not open automatically.Note
2.2.2. Opening a Console to a Virtual Machine
Procedure 2.3. Connecting to Virtual Machines
- Install Remote Viewer if it is not already installed. See Section 1.4.1, “Installing Console Components”.
- Click the Virtual Machines tab and select a virtual machine.
- Click the console button or right-click the virtual machine and select Console.
- If the connection protocol is set to SPICE, a console window will automatically open for the virtual machine.
- If the connection protocol is set to VNC, a
console.vvfile will be downloaded. Click on the file and a console window will automatically open for the virtual machine.
Note
2.2.3. Opening a Serial Console to a Virtual Machine
Important
engine-setup on new installations. The serial console relies on the ovirt-vmconsole package and the ovirt-vmconsole-proxy on the Manager, and the ovirt-vmconsole package and the ovirt-vmconsole-host package on virtualization hosts. These packages are installed by default on new installations. To install the packages on existing installations, reinstall the host. See Reinstalling Hosts in the Administration Guide.Procedure 2.4. Connecting to a Virtual Machine Serial Console
- On the client machine from which you will access the virtual machine serial console, generate an SSH key pair. The Manager supports standard SSH key types. For example, generate an RSA key:
# ssh-keygen -t rsa -b 2048 -C "admin@internal" -f .ssh/serialconsolekey
This command generates a public key and a private key. - In the Administration Portal or the User Portal, click the name of the signed-in user on the header bar, and then click to open the Edit Options window.
- In the User's Public Key text field, paste the public key of the client machine that will be used to access the serial console.
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- In the Console tab of the Edit Virtual Machine window, select the Enable VirtIO serial console check box.
- On the client machine, connect to the virtual machine's serial console:
- If a single virtual machine is available, this command connects the user to that virtual machine:
# ssh -t -p 2222 ovirt-vmconsole@MANAGER_IP Red Hat Enterprise Linux Server release 6.7 (Santiago) Kernel 2.6.32-573.3.1.el6.x86_64 on an x86_64 USER login:
If more than one virtual machine is available, this command lists the available virtual machines:# ssh -t -p 2222 ovirt-vmconsole@MANAGER_IP 1. vm1 [vmid1] 2. vm2 [vmid2] 3. vm3 [vmid3] > 2 Red Hat Enterprise Linux Server release 6.7 (Santiago) Kernel 2.6.32-573.3.1.el6.x86_64 on an x86_64 USER login:
Enter the number of the machine to which you want to connect, and press Enter. - Alternatively, connect directly to a virtual machine using its unique identifier or its name:
# ssh -t -p 2222 ovirt-vmconsole@MANAGER_IP --vm-id vmid1
# ssh -t -p 2222 ovirt-vmconsole@MANAGER_IP --vm-name vm1
Important
2.2.4. Automatically Connecting to a Virtual Machine
Procedure 2.5. Automatically Connecting to a Virtual Machine
- Click the name of the signed-in user on the header bar then click Options to open the Edit Options window.
- Click the Automatically Connect check box.
- Click OK.
2.3. Subscribing to the Required Entitlements
Procedure 2.6. Subscribing to the Required Entitlements Using Subscription Manager
- Register your system with the Content Delivery Network, entering your Customer Portal user name and password when prompted:
# subscription-manager register
- Locate the relevant subscription pools and note down the pool identifiers.
# subscription-manager list --available
- Use the pool identifiers located in the previous step to attach the required entitlements.
# subscription-manager attach --pool=pool_id
- Disable all existing repositories:
# subscription-manager repos --disable=*
- When a system is subscribed to a subscription pool with multiple repositories, only the main repository is enabled by default. Others are available, but disabled. Enable any additional repositories:
# subscription-manager repos --enable=repository
- Ensure that all packages currently installed are up to date:
# yum update
2.4. Installing Guest Agents and Drivers
2.4.1. Red Hat Virtualization Guest Agents and Drivers
Table 2.1. Red Hat Virtualization Guest Drivers
Driver | Description | Works on |
|---|---|---|
virtio-net | Paravirtualized network driver provides enhanced performance over emulated devices like rtl. | Server and Desktop. |
virtio-block | Paravirtualized HDD driver offers increased I/O performance over emulated devices like IDE by optimizing the coordination and communication between the guest and the hypervisor. The driver complements the software implementation of the virtio-device used by the host to play the role of a hardware device. | Server and Desktop. |
virtio-scsi | Paravirtualized iSCSI HDD driver offers similar functionality to the virtio-block device, with some additional enhancements. In particular, this driver supports adding hundreds of devices, and names devices using the standard SCSI device naming scheme. | Server and Desktop. |
virtio-serial | Virtio-serial provides support for multiple serial ports. The improved performance is used for fast communication between the guest and the host that avoids network complications. This fast communication is required for the guest agents and for other features such as clipboard copy-paste between the guest and the host and logging. | Server and Desktop. |
virtio-balloon | Virtio-balloon is used to control the amount of memory a guest actually accesses. It offers improved memory over-commitment. The balloon drivers are installed for future compatibility but not used by default in Red Hat Virtualization. | Server and Desktop. |
qxl | A paravirtualized display driver reduces CPU usage on the host and provides better performance through reduced network bandwidth on most workloads. | Server and Desktop. |
Table 2.2. Red Hat Virtualization Guest Agents and Tools
Guest agent/tool | Description | Works on |
|---|---|---|
rhevm-guest-agent-common | Allows the Red Hat Virtualization Manager to receive guest internal events and information such as IP address and installed applications. Also allows the Manager to execute specific commands, such as shut down or reboot, on a guest. On Red Hat Enterprise Linux 6 and higher guests, the rhevm-guest-agent-common installs tuned on your virtual machine and configures it to use an optimized, virtualized-guest profile. | Server and Desktop. |
spice-agent | The SPICE agent supports multiple monitors and is responsible for client-mouse-mode support to provide a better user experience and improved responsiveness than the QEMU emulation. Cursor capture is not needed in client-mouse-mode. The SPICE agent reduces bandwidth usage when used over a wide area network by reducing the display level, including color depth, disabling wallpaper, font smoothing, and animation. The SPICE agent enables clipboard support allowing cut and paste operations for both text and images between client and guest, and automatic guest display setting according to client-side settings. On Windows guests, the SPICE agent consists of vdservice and vdagent. | Server and Desktop. |
rhev-sso | An agent that enables users to automatically log in to their virtual machines based on the credentials used to access the Red Hat Virtualization Manager. | Desktop. |
rhev-usb | A component that contains drivers and services for Legacy USB support (version 3.0 and earlier) on guests. It is needed for accessing a USB device that is plugged into the client machine. RHEV-USB Client is needed on the client side.Important The Legacy USB option has been deprecated and will be removed in Red Hat Virtualization 4.1. | Desktop. |
2.4.2. Installing the Guest Agents and Drivers on Red Hat Enterprise Linux
Procedure 2.7. Installing the Guest Agents and Drivers on Red Hat Enterprise Linux
- Log in to the Red Hat Enterprise Linux virtual machine.
- Enable the Red Hat Virtualization Agent repository:
- For Red Hat Enterprise Linux 6
# subscription-manager repos --enable=rhel-6-server-rhv-4-agent-rpms
- For Red Hat Enterprise Linux 7
# subscription-manager repos --enable=rhel-7-server-rh-common-rpms
- Install the rhevm-guest-agent-common package and dependencies:
# yum install rhevm-guest-agent-common
- Start and enable the service:
- For Red Hat Enterprise Linux 6
# service ovirt-guest-agent start # chkconfig ovirt-guest-agent on
- For Red Hat Enterprise Linux 7
# systemctl start ovirt-guest-agent.service # systemctl enable ovirt-guest-agent.service
- Start and enable the
qemu-gaservice:- For Red Hat Enterprise Linux 6
# service qemu-ga start # chkconfig qemu-ga on
- For Red Hat Enterprise Linux 7
# systemctl start qemu-guest-agent.service # systemctl enable qemu-guest-agent.service
ovirt-guest-agent that you can configure via the ovirt-guest-agent.conf configuration file in the /etc/ directory.Chapter 3. Installing Windows Virtual Machines
- Create a blank virtual machine on which to install an operating system.
- Add a virtual disk for storage.
- Add a network interface to connect the virtual machine to the network.
- Attach the
virtio-win.vfddiskette to the virtual machine so that VirtIO-optimized device drivers can be installed during the operating system installation. - Install an operating system on the virtual machine. See your operating system's documentation for instructions.
- Install guest agents and drivers for additional virtual machine functionality.
3.1. Creating a Windows Virtual Machine
Procedure 3.1. Creating Windows Virtual Machines
- Click the tab.
- Click the button to open the New Virtual Machine window.
- Select a Windows variant from the Operating System drop-down list.
- Enter a Name for the virtual machine.
- Add storage to the virtual machine. or a virtual disk under Instance Images.
- Click and select an existing virtual disk.
- Click and enter a Size(GB) and Alias for a new virtual disk. You can accept the default settings for all other fields, or change them if required. See Section A.3, “Explanation of Settings in the New Virtual Disk and Edit Virtual Disk Windows” for more details on the fields for all disk types.
- Click .
- Connect the virtual machine to the network. Add a network interface by selecting a vNIC profile from the nic1 drop-down list at the bottom of the General tab.
- Specify the virtual machine's Memory Size on the System tab.
- Choose the First Device that the virtual machine will boot from on the Boot Options tab.
- You can accept the default settings for all other fields, or change them if required. For more details on all fields in the New Virtual Machine window, see Section A.1, “Explanation of Settings in the New Virtual Machine and Edit Virtual Machine Windows”.
- Click .
Down. Before you can use this virtual machine, you must install an operating system and VirtIO-optimized disk and network drivers.3.2. Starting the Virtual Machine Using the Run Once Option
3.2.1. Installing Windows on VirtIO-Optimized Hardware
virtio-win.vfd diskette to your virtual machine. These drivers provide a performance improvement over emulated device drivers.Red Hat VirtIO network interface and a disk that uses the VirtIO interface to your virtual machine.Note
virtio-win.vfd diskette is placed automatically on ISO storage domains that are hosted on the Manager server. An administrator must manually upload it to other ISO storage domains using the engine-iso-uploader tool.Procedure 3.2. Installing VirtIO Drivers during Windows Installation
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Expand the Boot Options menu.
- Select the Attach Floppy check box, and select
virtio-win.vfdfrom the drop-down list. - Select the Attach CD check box, and select the required Windows ISO from the drop-down list.
- Move CD-ROM to the top of the Boot Sequence field.
- Configure the rest of your Run Once options as required. See Section A.5, “Explanation of Settings in the Run Once Window” for more details.
- Click OK.
Up, and the operating system installation begins. Open a console to the virtual machine if one does not open automatically.virtio-win.vfd diskette that was attached to your virtual machine as A:. For each supported virtual machine architecture and Windows version, there is a folder on the disk containing optimized hardware device drivers.3.2.2. Opening a Console to a Virtual Machine
Procedure 3.3. Connecting to Virtual Machines
- Install Remote Viewer if it is not already installed. See Section 1.4.1, “Installing Console Components”.
- Click the Virtual Machines tab and select a virtual machine.
- Click the console button or right-click the virtual machine and select Console.
- If the connection protocol is set to SPICE, a console window will automatically open for the virtual machine.
- If the connection protocol is set to VNC, a
console.vvfile will be downloaded. Click on the file and a console window will automatically open for the virtual machine.
Note
3.3. Installing Guest Agents and Drivers
3.3.1. Red Hat Virtualization Guest Agents and Drivers
Table 3.1. Red Hat Virtualization Guest Drivers
Driver | Description | Works on |
|---|---|---|
virtio-net | Paravirtualized network driver provides enhanced performance over emulated devices like rtl. | Server and Desktop. |
virtio-block | Paravirtualized HDD driver offers increased I/O performance over emulated devices like IDE by optimizing the coordination and communication between the guest and the hypervisor. The driver complements the software implementation of the virtio-device used by the host to play the role of a hardware device. | Server and Desktop. |
virtio-scsi | Paravirtualized iSCSI HDD driver offers similar functionality to the virtio-block device, with some additional enhancements. In particular, this driver supports adding hundreds of devices, and names devices using the standard SCSI device naming scheme. | Server and Desktop. |
virtio-serial | Virtio-serial provides support for multiple serial ports. The improved performance is used for fast communication between the guest and the host that avoids network complications. This fast communication is required for the guest agents and for other features such as clipboard copy-paste between the guest and the host and logging. | Server and Desktop. |
virtio-balloon | Virtio-balloon is used to control the amount of memory a guest actually accesses. It offers improved memory over-commitment. The balloon drivers are installed for future compatibility but not used by default in Red Hat Virtualization. | Server and Desktop. |
qxl | A paravirtualized display driver reduces CPU usage on the host and provides better performance through reduced network bandwidth on most workloads. | Server and Desktop. |
Table 3.2. Red Hat Virtualization Guest Agents and Tools
Guest agent/tool | Description | Works on |
|---|---|---|
rhevm-guest-agent-common | Allows the Red Hat Virtualization Manager to receive guest internal events and information such as IP address and installed applications. Also allows the Manager to execute specific commands, such as shut down or reboot, on a guest. On Red Hat Enterprise Linux 6 and higher guests, the rhevm-guest-agent-common installs tuned on your virtual machine and configures it to use an optimized, virtualized-guest profile. | Server and Desktop. |
spice-agent | The SPICE agent supports multiple monitors and is responsible for client-mouse-mode support to provide a better user experience and improved responsiveness than the QEMU emulation. Cursor capture is not needed in client-mouse-mode. The SPICE agent reduces bandwidth usage when used over a wide area network by reducing the display level, including color depth, disabling wallpaper, font smoothing, and animation. The SPICE agent enables clipboard support allowing cut and paste operations for both text and images between client and guest, and automatic guest display setting according to client-side settings. On Windows guests, the SPICE agent consists of vdservice and vdagent. | Server and Desktop. |
rhev-sso | An agent that enables users to automatically log in to their virtual machines based on the credentials used to access the Red Hat Virtualization Manager. | Desktop. |
rhev-usb | A component that contains drivers and services for Legacy USB support (version 3.0 and earlier) on guests. It is needed for accessing a USB device that is plugged into the client machine. RHEV-USB Client is needed on the client side.Important The Legacy USB option has been deprecated and will be removed in Red Hat Virtualization 4.1. | Desktop. |
3.3.2. Installing the Guest Agents and Drivers on Windows
rhev-tools-setup.iso ISO file, which is provided by the rhev-guest-tools-iso package installed as a dependency to the Red Hat Virtualization Manager. This ISO file is located in /usr/share/rhev-guest-tools-iso/rhev-tools-setup.iso on the system on which the Red Hat Virtualization Manager is installed.Note
rhev-tools-setup.iso ISO file is automatically copied to the default ISO storage domain, if any, when you run engine-setup, or must be manually uploaded to an ISO storage domain.Note
rhev-tools-setup.iso ISO file must be manually attached to running Windows virtual machines to install updated versions of the tools and drivers. If the APT service is enabled on virtual machines, the updated ISO files will be automatically attached.Note
ISSILENTMODE and ISNOREBOOT to RHEV-toolsSetup.exe to silently install the guest agents and drivers and prevent the machine on which they have been installed from rebooting immediately after installation. The machine can then be rebooted later once the deployment process is complete.D:\RHEV-toolsSetup.exe ISSILENTMODE ISNOREBOOT
Procedure 3.4. Installing the Guest Agents and Drivers on Windows
- Log in to the virtual machine.
- Select the CD Drive containing the
rhev-tools-setup.isofile. - Double-click RHEV-toolsSetup.
- Click at the welcome screen.
- Follow the prompts on the RHEV-Tools InstallShield Wizard window. Ensure all check boxes in the list of components are selected.
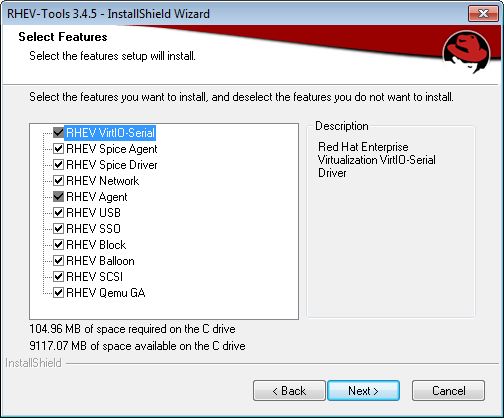
Figure 3.2. Selecting All Components of Red Hat Virtualization Tools for Installation
- Once installation is complete, select
Yes, I want to restart my computer nowand click to apply the changes.
RHEV Agent that you can configure using the rhev-agent configuration file located in C:\Program Files\Redhat\RHEV\Drivers\Agent.3.3.3. Automating Guest Additions on Windows Guests with Red Hat Virtualization Application Provisioning Tool(APT)
rhev-tools-setup.iso ISO file to the virtual machine.Procedure 3.5. Installing the APT Service on Windows
- Log in to the virtual machine.
- Select the CD Drive containing the
rhev-tools-setup.isofile. - Double-click RHEV-Application Provisioning Tool.
- Click in the User Account Control window.
- Once installation is complete, ensure the
Start RHEV-apt Servicecheck box is selected in the RHEV-Application Provisioning Tool InstallShield Wizard window, and click to apply the changes.
Note
Start RHEV-apt Service check box. You can stop, start, or restart the service at any time using the Services window.Chapter 4. Additional Configuration
4.1. Configuring Single Sign-On for Virtual Machines
Important
4.1.1. Configuring Single Sign-On for Red Hat Enterprise Linux Virtual Machines Using IPA (IdM)
Important
Procedure 4.1. Configuring Single Sign-On for Red Hat Enterprise Linux Virtual Machines
- Log in to the Red Hat Enterprise Linux virtual machine.
- Enable the required channel:
- For Red Hat Enterprise Linux 6
# subscription-manager repos --enable=rhel-6-server-rhv-4-agent-rpms
- For Red Hat Enterprise Linux 7
# subscription-manager repos --enable=rhel-7-server-rh-common-rpms
- Download and install the guest agent packages:
# yum install rhevm-guest-agent-common
- Install the single sign-on packages:
# yum install rhevm-guest-agent-pam-module # yum install rhevm-guest-agent-gdm-plugin
- Install the IPA packages:
# yum install ipa-client
- Run the following command and follow the prompts to configure ipa-client and join the virtual machine to the domain:
# ipa-client-install --permit --mkhomedir
Note
In environments that use DNS obfuscation, this command should be:# ipa-client-install --domain=FQDN --server==FQDN
- For Red Hat Enterprise Linux 7.2 or later, run:
# authconfig --enablenis --update
Note
Red Hat Enterprise Linux 7.2 or later has a new version of the System Security Services Daemon (SSSD) which introduces configuration that is incompatible with the Red Hat Virtualization Manager guest agent single sign-on implementation. The command will ensure that single sign-on works. - Fetch the details of an IPA user:
# getent passwd IPA_user_name
This will return something like this:some-ipa-user:*:936600010:936600001::/home/some-ipa-user:/bin/sh
You will need this information in the next step to create a home directory for some-ipa-user. - Set up a home directory for the IPA user:
- Create the new user's home directory:
# mkdir /home/some-ipa-user
- Give the new user ownership of the new user's home directory:
# chown 935500010:936600001 /home/some-ipa-user
4.1.2. Configuring Single Sign-On for Red Hat Enterprise Linux Virtual Machines Using Active Directory
Important
Procedure 4.2. Configuring Single Sign-On for Red Hat Enterprise Linux Virtual Machines
- Log in to the Red Hat Enterprise Linux virtual machine.
- Enable the Red Hat Virtualization Agent channel:
- For Red Hat Enterprise Linux 6
# subscription-manager repos --enable=rhel-6-server-rhv-4-agent-rpms
- For Red Hat Enterprise Linux 7
# subscription-manager repos --enable=rhel-7-server-rh-common-rpms
- Download and install the guest agent packages:
# yum install rhevm-guest-agent-common
- Install the single sign-on packages:
# yum install rhev-agent-gdm-plugin-rhevcred
- Install the Samba client packages:
# yum install samba-client samba-winbind samba-winbind-clients
- On the virtual machine, modify the
/etc/samba/smb.conffile to contain the following, replacingDOMAINwith the short domain name andREALM.LOCALwith the Active Directory realm:[global] workgroup = DOMAIN realm = REALM.LOCAL log level = 2 syslog = 0 server string = Linux File Server security = ads log file = /var/log/samba/%m max log size = 50 printcap name = cups printing = cups winbind enum users = Yes winbind enum groups = Yes winbind use default domain = true winbind separator = + idmap uid = 1000000-2000000 idmap gid = 1000000-2000000 template shell = /bin/bash
- Join the virtual machine to the domain:
net ads join -U user_name
- Start the winbind service and ensure it starts on boot:
- For Red Hat Enterprise Linux 6
# service winbind start # chkconfig winbind on
- For Red Hat Enterprise Linux 7
# systemctl start winbind.service # systemctl enable winbind.service
- Verify that the system can communicate with Active Directory:
- Verify that a trust relationship has been created:
# wbinfo -t
- Verify that you can list users:
# wbinfo -u
- Verify that you can list groups:
# wbinfo -g
- Configure the NSS and PAM stack:
- Open the Authentication Configuration window:
# authconfig-tui
- Select the Use Winbind check box, select Next and press Enter.
- Select the OK button and press Enter.
4.1.3. Configuring Single Sign-On for Windows Virtual Machines
RHEV Guest Tools ISO file provides this agent. If the RHEV-toolsSetup.iso image is not available in your ISO domain, contact your system administrator.Procedure 4.3. Configuring Single Sign-On for Windows Virtual Machines
- Select the Windows virtual machine. Ensure the machine is powered up.
- Click Change CD.
- Select
RHEV-toolsSetup.isofrom the list of images. - Click OK.
- Click the Console icon and log in to the virtual machine.
- On the virtual machine, locate the CD drive to access the contents of the guest tools ISO file and launch
RHEV-ToolsSetup.exe. After the tools have been installed, you will be prompted to restart the machine to apply the changes.
4.1.4. Disabling Single Sign-on for Virtual Machines
Procedure 4.4. Disabling Single Sign-On for Virtual Machines
- Select a virtual machine and click .
- Click the Console tab.
- Select the Disable Single Sign On check box.
- Click .
4.2. Configuring USB Devices
Important
4.2.1. Using USB Devices on Virtual Machines
- Client
- Red Hat Enterprise Linux 7.1 and higher
- Red Hat Enterprise Linux 6.0 and higher
- Windows 10
- Windows 8
- Windows 7
- Windows 2008
- Windows 2008 Server R2
- Guest
- Red Hat Enterprise Linux 7.1 and higher
- Red Hat Enterprise Linux 6.0 and higher
- Windows 7
- Windows XP
- Windows 2008
Note
4.2.2. Using USB Devices on a Windows Client
Procedure 4.5. Using USB Devices on a Windows Client
- When the usbdk driver is installed, select a virtual machine that has been configured to use the SPICE protocol.
- Ensure USB support is set to Native:
- Click Edit.
- Click the Console tab.
- Select Native from the USB Support drop-down list.
- Click OK.
- Click the button and select the Enable USB Auto-Share check box.
- Start the virtual machine and click the button to connect to that virtual machine. When you plug your USB device into the client machine, it will automatically be redirected to appear on your guest machine.
4.2.3. Using USB Devices on a Red Hat Enterprise Linux Client
Procedure 4.6. Using USB devices on a Red Hat Enterprise Linux client
- Click the Virtual Machines tab and select a virtual machine that has been configured to use the SPICE protocol.
- Ensure USB support is set to Native:
- Click Edit.
- Click the Console tab.
- Select Native from the USB Support drop-down list.
- Click OK.
- Click the button and select the Enable USB Auto-Share check box.
- Start the virtual machine and click the button to connect to that virtual machine. When you plug your USB device into the client machine, it will automatically be redirected to appear on your guest machine.
4.3. Configuring Multiple Monitors
4.3.1. Configuring Multiple Displays for Red Hat Enterprise Linux Virtual Machines
- Start a SPICE session with the virtual machine.
- Open the View drop-down menu at the top of the SPICE client window.
- Open the Display menu.
- Click the name of a display to enable or disable that display.
Note
By default, Display 1 is the only display that is enabled on starting a SPICE session with a virtual machine. If no other displays are enabled, disabling this display will close the session.
4.3.2. Configuring Multiple Displays for Windows Virtual Machines
- Click the Virtual Machines tab and select a virtual machine.
- With the virtual machine in a powered-down state, click Edit.
- Click the Console tab.
- Select the number of displays from the Monitors drop-down list.
Note
This setting controls the maximum number of displays that can be enabled for the virtual machine. While the virtual machine is running, additional displays can be enabled up to this number. - Click Ok.
- Start a SPICE session with the virtual machine.
- Open the View drop-down menu at the top of the SPICE client window.
- Open the Display menu.
- Click the name of a display to enable or disable that display.
Note
By default, Display 1 is the only display that is enabled on starting a SPICE session with a virtual machine. If no other displays are enabled, disabling this display will close the session.
4.4. Configuring Console Options
4.4.1. Console Options
Simple Protocol for Independent Computing Environments (SPICE) is the recommended connection protocol for both Linux virtual machines and Windows virtual machines. To open a console to a virtual machine using SPICE, use Remote Viewer.
Virtual Network Computing (VNC) can be used to open consoles to both Linux virtual machines and Windows virtual machines. To open a console to a virtual machine using VNC, use Remote Viewer or a VNC client.
Remote Desktop Protocol (RDP) can only be used to open consoles to Windows virtual machines, and is only available when you access a virtual machines from a Windows machine on which Remote Desktop has been installed. Before you can connect to a Windows virtual machine using RDP, you must set up remote sharing on the virtual machine and configure the firewall to allow remote desktop connections.
Note
4.4.1.1. Accessing Console Options
Procedure 4.7. Accessing Console Options
- Select a running virtual machine.
- Open the Console Options window.
- In the Administration Portal, right-click the virtual machine and click Console Options.
- In the User Portal, click the Edit Console Options button.
Note
4.4.1.2. SPICE Console Options
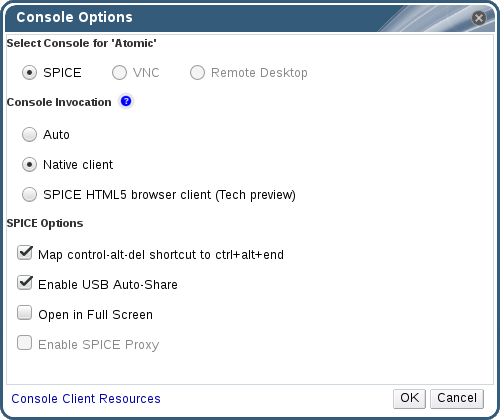
Figure 4.2. The Console Options window
Console Invocation
- Auto: The Manager automatically selects the method for invoking the console.
- Native client: When you connect to the console of the virtual machine, a file download dialog provides you with a file that opens a console to the virtual machine via Remote Viewer.
- SPICE HTML5 browser client (Tech preview): When you connect to the console of the virtual machine, a browser tab is opened that acts as the console.
SPICE Options
- Map control-alt-del shortcut to ctrl+alt+end: Select this check box to map the Ctrl+Alt+Del key combination to Ctrl+Alt+End inside the virtual machine.
- Enable USB Auto-Share: Select this check box to automatically redirect USB devices to the virtual machine. If this option is not selected, USB devices will connect to the client machine instead of the guest virtual machine. To use the USB device on the guest machine, manually enable it in the SPICE client menu.
- Open in Full Screen: Select this check box for the virtual machine console to automatically open in full screen when you connect to the virtual machine. Press SHIFT+F11 to toggle full screen mode on or off.
- Enable SPICE Proxy: Select this check box to enable the SPICE proxy.
- Enable WAN options: Select this check box to set the parameters
WANDisableEffectsandWANColorDepthtoanimationand16bits respectively on Windows virtual machines. Bandwidth in WAN environments is limited and this option prevents certain Windows settings from consuming too much bandwidth.
4.4.1.3. VNC Console Options
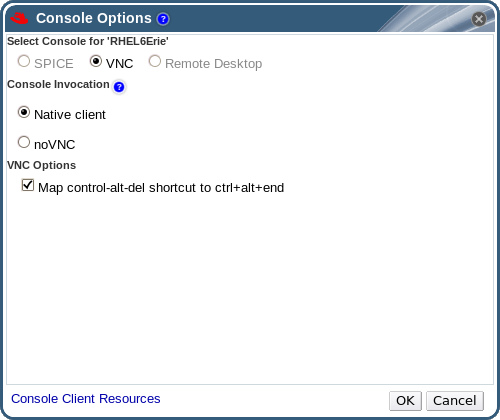
Figure 4.3. The Console Options window
Console Invocation
- Native Client: When you connect to the console of the virtual machine, a file download dialog provides you with a file that opens a console to the virtual machine via Remote Viewer.
- noVNC: When you connect to the console of the virtual machine, a browser tab is opened that acts as the console.
VNC Options
- Map control-alt-delete shortcut to ctrl+alt+end: Select this check box to map the Ctrl+Alt+Del key combination to Ctrl+Alt+End inside the virtual machine.
4.4.1.4. RDP Console Options
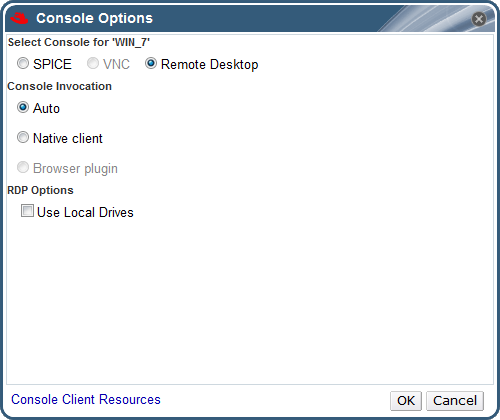
Figure 4.4. The Console Options window
Console Invocation
- Auto: The Manager automatically selects the method for invoking the console.
- Native client: When you connect to the console of the virtual machine, a file download dialog provides you with a file that opens a console to the virtual machine via Remote Desktop.
RDP Options
- Use Local Drives: Select this check box to make the drives on the client machine accessible on the guest virtual machine.
4.4.2. Remote Viewer Options
4.4.2.1. Remote Viewer Options
4.4.2.2. Remote Viewer Hotkeys
Note
4.4.2.3. Manually Associating console.vv Files with Remote Viewer
console.vv file when attempting to open a console to a virtual machine using the native client console option, and Remote Viewer is already installed, then you can manually associate console.vv files with Remote Viewer so that Remote Viewer can automatically use those files to open consoles.Procedure 4.8. Manually Associating console.vv Files with Remote Viewer
- Start the virtual machine.
- Open the Console Options window.
- In the Administration Portal, right-click the virtual machine and click Console Options.
- In the User Portal, click the Edit Console Options button.
- Change the console invocation method to Native client and click .
- Attempt to open a console to the virtual machine, then click when prompted to open or save the
console.vvfile. - Navigate to the location on your local machine where you saved the file.
- Double-click the
console.vvfile and select when prompted. - In the Open with window, select and click the button.
- Navigate to the
C:\Users\[user name]\AppData\Local\virt-viewer\bindirectory and selectremote-viewer.exe. - Click and then click .
console.vv file that the Red Hat Virtualization Manager provides to open a console to that virtual machine without prompting you to select the application to use.4.5. Configuring a Watchdog
4.5.1. Adding a Watchdog Card to a Virtual Machine
Procedure 4.9. Adding Watchdog Cards to Virtual Machines
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Click the High Availability tab.
- Select the watchdog model to use from the Watchdog Model drop-down list.
- Select an action from the Watchdog Action drop-down list. This is the action that the virtual machine takes when the watchdog is triggered.
- Click .
4.5.2. Installing a Watchdog
watchdog service.Procedure 4.10. Installing Watchdogs
- Log in to the virtual machine on which the watchdog card is attached.
- Install the watchdog package and dependencies:
# yum install watchdog
- Edit the
/etc/watchdog.conffile and uncomment the following line:watchdog-device = /dev/watchdog
- Save the changes.
- Start the
watchdogservice and ensure this service starts on boot:- Red Hat Enterprise Linux 6:
# service watchdog start # chkconfig watchdog on
- Red Hat Enterprise Linux 7:
# systemctl start watchdog.service # systemctl enable watchdog.service
4.5.3. Confirming Watchdog Functionality
watchdog service is active.Warning
Procedure 4.11. Confirming Watchdog Functionality
- Log in to the virtual machine on which the watchdog card is attached.
- Confirm that the watchdog card has been identified by the virtual machine:
# lspci | grep watchdog -i
- Run one of the following commands to confirm that the watchdog is active:
- Trigger a kernel panic:
# echo c > /proc/sysrq-trigger
- Terminate the
watchdogservice:# kill -9 `pgrep watchdog`
4.5.4. Parameters for Watchdogs in watchdog.conf
watchdog service available in the /etc/watchdog.conf file. To configure an option, you must uncomment that option and restart the watchdog service after saving the changes.Note
watchdog service and using the watchdog command, see the watchdog man page.Table 4.2. watchdog.conf variables
| Variable name | Default Value | Remarks |
|---|---|---|
ping | N/A | An IP address that the watchdog attempts to ping to verify whether that address is reachable. You can specify multiple IP addresses by adding additional ping lines. |
interface | N/A | A network interface that the watchdog will monitor to verify the presence of network traffic. You can specify multiple network interfaces by adding additional interface lines. |
file | /var/log/messages | A file on the local system that the watchdog will monitor for changes. You can specify multiple files by adding additional file lines. |
change | 1407 | The number of watchdog intervals after which the watchdog checks for changes to files. A change line must be specified on the line directly after each file line, and applies to the file line directly above that change line. |
max-load-1 | 24 | The maximum average load that the virtual machine can sustain over a one-minute period. If this average is exceeded, then the watchdog is triggered. A value of 0 disables this feature. |
max-load-5 | 18 | The maximum average load that the virtual machine can sustain over a five-minute period. If this average is exceeded, then the watchdog is triggered. A value of 0 disables this feature. By default, the value of this variable is set to a value approximately three quarters that of max-load-1. |
max-load-15 | 12 | The maximum average load that the virtual machine can sustain over a fifteen-minute period. If this average is exceeded, then the watchdog is triggered. A value of 0 disables this feature. By default, the value of this variable is set to a value approximately one half that of max-load-1. |
min-memory | 1 | The minimum amount of virtual memory that must remain free on the virtual machine. This value is measured in pages. A value of 0 disables this feature. |
repair-binary | /usr/sbin/repair | The path and file name of a binary file on the local system that will be run when the watchdog is triggered. If the specified file resolves the issues preventing the watchdog from resetting the watchdog counter, then the watchdog action is not triggered. |
test-binary | N/A | The path and file name of a binary file on the local system that the watchdog will attempt to run during each interval. A test binary allows you to specify a file for running user-defined tests. |
test-timeout | N/A | The time limit, in seconds, for which user-defined tests can run. A value of 0 allows user-defined tests to continue for an unlimited duration. |
temperature-device | N/A | The path to and name of a device for checking the temperature of the machine on which the watchdog service is running. |
max-temperature | 120 | The maximum allowed temperature for the machine on which the watchdog service is running. The machine will be halted if this temperature is reached. Unit conversion is not taken into account, so you must specify a value that matches the watchdog card being used. |
admin | root | The email address to which email notifications are sent. |
interval | 10 | The interval, in seconds, between updates to the watchdog device. The watchdog device expects an update at least once every minute, and if there are no updates over a one-minute period, then the watchdog is triggered. This one-minute period is hard-coded into the drivers for the watchdog device, and cannot be configured. |
logtick | 1 | When verbose logging is enabled for the watchdog service, the watchdog service periodically writes log messages to the local system. The logtick value represents the number of watchdog intervals after which a message is written. |
realtime | yes | Specifies whether the watchdog is locked in memory. A value of yes locks the watchdog in memory so that it is not swapped out of memory, while a value of no allows the watchdog to be swapped out of memory. If the watchdog is swapped out of memory and is not swapped back in before the watchdog counter reaches zero, then the watchdog is triggered. |
priority | 1 | The schedule priority when the value of realtime is set to yes. |
pidfile | /var/run/syslogd.pid | The path and file name of a PID file that the watchdog monitors to see if the corresponding process is still active. If the corresponding process is not active, then the watchdog is triggered. |
4.6. Configuring Virtual NUMA
numactl --hardware. The output of this command should show at least two NUMA nodes. You can also view the host's NUMA topology in the Administration Portal by selecting the host from the Hosts tab and clicking . This button is only available when the selected host has at least two NUMA nodes.Procedure 4.12. Configuring Virtual NUMA
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Click the Host tab.
- Select the Specific radio button and select a host from the list. The selected host must have at least two NUMA nodes.
- Select Do not allow migration from the Migration Options drop-down list.
- Enter a number into the NUMA Node Count field to assign virtual NUMA nodes to the virtual machine.
- Select Strict, Preferred, or Interleave from the Tune Mode drop-down list. If the selected mode is Preferred, the NUMA Node Count must be set to
1. - Click .
- In the NUMA Topology window, click and drag virtual NUMA nodes from the box on the right to host NUMA nodes on the left as required, and click .
- Click .
Note
4.7. Configuring Red Hat Satellite Errata Management for a Virtual Machine
- The host that the virtual machine runs on also needs to be configured to receive errata information from Satellite. See Configuring Satellite Errata Management for a Host in the Administration Guide for more information.
- The virtual machine must have the rhevm-guest-agent package installed. This package allows the virtual machine to report its host name to the Red Hat Virtualization Manager. This allows the Red Hat Satellite server to identify the virtual machine as a content host and report the applicable errata. For more information on installing the ovirt-guest-agent package see Section 2.4.2, “Installing the Guest Agents and Drivers on Red Hat Enterprise Linux” for Red Hat Enterprise Linux virtual machines and Section 3.3.2, “Installing the Guest Agents and Drivers on Windows” for Windows virtual machines.
Important
Procedure 4.13. Configuring Red Hat Satellite Errata Management
Note
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Click the Foreman/Satellite tab.
- Select the required Satellite server from the Provider drop-down list.
- Click .
Chapter 5. Editing Virtual Machines
5.1. Editing Virtual Machine Properties
Procedure 5.1. Editing Virtual Machines
- Select the virtual machine to be edited.
- Click .
- Change settings as required.Changes to the following settings are applied immediately:
- Name
- Description
- Comment
- Optimized for (Desktop/Server)
- Delete Protection
- Network Interfaces
- Memory Size (Edit this field to hot plug virtual memory. See Section 5.5, “Hot Plugging Virtual Memory”.)
- Virtual Sockets (Edit this field to hot plug CPUs. See Section 5.6, “Hot Plugging Virtual CPUs”.)
- Use custom migration downtime
- Highly Available
- Priority for Run/Migration queue
- Disable strict user checking
- Icon
- Click .
- If the Next Start Configuration pop-up window appears, click .
 ) appears as a reminder of the pending changes.
) appears as a reminder of the pending changes.5.2. Editing IO Threads
Procedure 5.2. Editing IO Threads
- Select the virtual machine to be edited.
- Click .
- Click the Resource Allocation tab.
- Select the IO Threads Enabled check box. Red Hat recommends using the default number of IO threads, which is
1. - Click .
- Click the Reboot icon to restart the virtual machine.If you increased the number of IO threads, you must reactivate the disks so that the disks will be remapped according to the correct number of controllers:
- Click the Shutdown icon to stop the virtual machine.
- Click the Disks tab in the details pane.
- Select each disk and click Deactivate.
- Select each disk and click Activate.
- Click the Run icon to start the virtual machine.
Procedure 5.3. Viewing Disk Controller Assignment
- Log in to the host machine.
- Use the
dumpxmlcommand to view the mapping of disks to controllers:# virsh -r dumpxml virtual_machine_name
5.3. Network Interfaces
5.3.1. Adding a New Network Interface
Procedure 5.4. Adding Network Interfaces to Virtual Machines
- Click the Virtual Machines tab and select a virtual machine.
- Click the Network Interfaces tab in the details pane.
- Click .
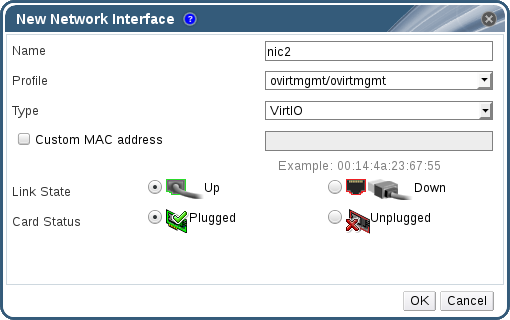
Figure 5.1. New Network Interface window
- Enter the Name of the network interface.
- Use the drop-down lists to select the Profile and the Type of the network interface. The Profile and Type drop-down lists are populated in accordance with the profiles and network types available to the cluster and the network interface cards available to the virtual machine.
- Select the Custom MAC address check box and enter a MAC address for the network interface card as required.
- Click .
5.3.2. Editing a Network Interface
Procedure 5.5. Editing Network Interfaces
- Click the Virtual Machines tab and select a virtual machine.
- Click the Network Interfaces tab in the details pane and select the network interface to edit.
- Click . The Edit Network Interface window contains the same fields as the New Network Interface window.
- Change settings as required.
- Click .
5.3.3. Hot Plugging a Network Interface
Note
Procedure 5.6. Hot Plugging Network Interfaces
- Click the Virtual Machines tab and select a virtual machine.
- Click the Network Interfaces tab in the details pane and select the network interface to hot plug.
- Click .
- Set the Card Status to Plugged to enable the network interface, or set it to Unplugged to disable the network interface.
- Click .
5.3.4. Removing a Network Interface
Procedure 5.7. Removing Network Interfaces
- Click the Virtual Machines tab and select a virtual machine.
- Click the Network Interfaces tab in the details pane and select the network interface to remove.
- Click .
- Click .
5.4. Virtual Disks
5.4.1. Adding a New Virtual Disk
Procedure 5.8. Adding Disks to Virtual Machines
- Click the Virtual Machines tab and select a virtual machine.
- Click the Disks tab in the details pane.
- Click .
- Use the appropriate radio buttons to switch between Image, Direct LUN, or Cinder. Virtual disks added in the User Portal can only be Image disks. Direct LUN and Cinder disks can be added in the Administration Portal.
- Enter a Size(GB), Alias, and Description for the new disk.
- Use the drop-down lists and check boxes to configure the disk. See Section A.3, “Explanation of Settings in the New Virtual Disk and Edit Virtual Disk Windows” for more details on the fields for all disk types.
- Click .
5.4.2. Attaching an Existing Disk to a Virtual Machine
Procedure 5.9. Attaching Virtual Disks to Virtual Machines
- Click the Virtual Machines tab and select a virtual machine.
- Click the Disks tab in the details pane.
- Click .
- Select one or more virtual disks from the list of available disks and select the required interface from the Interface drop-down.
- Click .
Note
5.4.3. Extending the Available Size of a Virtual Disk
fdisk utility to resize the partitions and file systems as required. See How to Resize a Partition using fdisk for more information.Procedure 5.10. Extending the Available Size of Virtual Disks
- Click the Virtual Machines tab and select a virtual machine.
- Click the Disks tab in the details pane and select the disk to edit.
- Click .
- Enter a value in the
Extend size by(GB)field. - Click .
locked for a short time, during which the drive is resized. When the resizing of the drive is complete, the status of the drive becomes OK.5.4.4. Hot Plugging a Virtual Disk
Note
Procedure 5.11. Hot Plugging Virtual Disks
- Click the Virtual Machines tab and select a virtual machine.
- Click the Disks tab in the details pane and select the virtual disk to hot plug.
- Click to enable the disk, or click to disable the disk.
- Click .
5.4.5. Removing a Virtual Disk from a Virtual Machine
Procedure 5.12. Removing Virtual Disks From Virtual Machines
- Click the Virtual Machines tab and select a virtual machine.
- Click the Disks tab in the details pane and select the virtual disk to remove.
- Click .
- Click .
- Click .
- Optionally, select the Remove Permanently check box to completely remove the virtual disk from the environment. If you do not select this option - for example, because the disk is a shared disk - the virtual disk will remain in the Disks resource tab.
- Click .
5.4.6. Importing a Disk Image from an Imported Storage Domain
Note
Procedure 5.13. Importing a Disk Image
- Select a storage domain that has been imported into the data center.
- In the details pane, click Disk Import.
- Select one or more disk images and click to open the Import Disk(s) window.
- Select the appropriate Disk Profile for each disk.
- Click to import the selected disks.
5.4.7. Importing an Unregistered Disk Image from an Imported Storage Domain
Note
Procedure 5.14. Importing a Disk Image
- Select a storage domain that has been imported into the data center.
- Right-click the storage domain and select Scan Disks so that the Manager can identify unregistered disks.
- In the details pane, click Disk Import.
- Select one or more disk images and click to open the Import Disk(s) window.
- Select the appropriate Disk Profile for each disk.
- Click to import the selected disks.
5.5. Hot Plugging Virtual Memory
Important
Procedure 5.15. Hot Plugging Virtual Memory
- Click the Virtual Machines tab and select a running virtual machine.
- Click .
- Click the System tab.
- Edit the Memory Size as required. Memory can be added in multiples of 256 MB.
- Click .This action opens the Next Start Configuration window, as the MemSizeMb value will not change until the virtual machine is restarted. However, the hot plug action is triggered by the change to the memory value, which can be applied immediately.
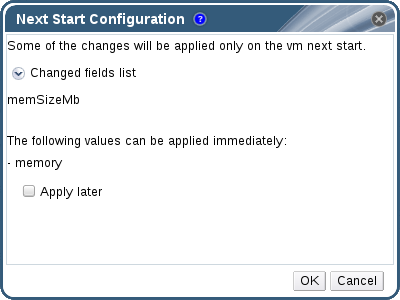
Figure 5.4. Hot Plug Virtual Memory
- Clear the Apply later check box to apply the change immediately.
- Click OK.
5.6. Hot Plugging Virtual CPUs
- The virtual machine's Operating System must be explicitly set in the New Virtual Machine window.
- The virtual machine's operating system must support CPU hot plug. See the table below for support details.
- Windows virtual machines must have the guest agents installed. See Section 3.3.2, “Installing the Guest Agents and Drivers on Windows”.
Important
Procedure 5.16. Hot Plugging Virtual CPUs
- Click the Virtual Machines tab and select a running virtual machine.
- Click .
- Click the System tab.
- In the Advanced Parameters section, change the value of Virtual Sockets as required.
- Click .
Table 5.1. Operating System Support Matrix for vCPU Hot Plug
Operating System | Version | Architecture | Hot Plug Supported |
|---|---|---|---|
Red Hat Enterprise Linux 6.3+ | x86 | Yes | |
Red Hat Enterprise Linux 7.0+ | x86 | Yes | |
Microsoft Windows Server 2008 | All | x86 | No |
Microsoft Windows Server 2008 | Standard, Enterprise | x64 | No |
Microsoft Windows Server 2008 | Datacenter | x64 | Yes |
Microsoft Windows Server 2008 R2 | All | x86 | No |
Microsoft Windows Server 2008 R2 | Standard, Enterprise | x64 | No |
Microsoft Windows Server 2008 R2 | Datacenter | x64 | Yes |
Microsoft Windows Server 2012 | All | x64 | Yes |
Microsoft Windows Server 2012 R2 | All | x64 | Yes |
Microsoft Windows 7 | All | x86 | No |
Microsoft Windows 7 | Starter, Home, Home Premium, Professional | x64 | No |
Microsoft Windows 7 | Enterprise, Ultimate | x64 | Yes |
Microsoft Windows 8.x | All | x86 | Yes |
Microsoft Windows 8.x | All | x64 | Yes |
5.7. Pinning a Virtual Machine to Multiple Hosts
Note
Procedure 5.17. Pinning Virtual Machines to Multiple Hosts
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Click the Host tab.
- Select the Specific radio button under Start Running On and select two or more hosts from the list.
- Select Do not allow migration from the Migration Options drop-down list.
- Click the High Availability tab.
- Select the Highly Available check box.
- Select Low, Medium, or High from the Priority drop-down list. When migration is triggered, a queue is created in which the high priority virtual machines are migrated first. If a cluster is running low on resources, only the high priority virtual machines are migrated.
- Click .
5.8. Changing the CD for a Virtual Machine
Note
Procedure 5.18. Changing the CD for a Virtual Machine
- Click the Virtual Machines tab and select a running virtual machine.
- Click .
- Select an option from the drop-down list:
- Select an ISO file from the list to eject the CD currently accessible to the virtual machine and mount that ISO file as a CD.
- Select from the list to eject the CD currently accessible to the virtual machine.
- Click .
5.9. Smart Card Authentication
Procedure 5.19. Enabling Smart Cards
- Ensure that the smart card hardware is plugged into the client machine and is installed according to manufacturer's directions.
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Click the tab and select the check box.
- Click .
- Connect to the running virtual machine by clicking the icon. Smart card authentication is now passed from the client hardware to the virtual machine.
Important
Procedure 5.20. Disabling Smart Cards
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Click the tab, and clear the check box.
- Click .
Procedure 5.21. Configuring Client Systems for Smart Card Sharing
- Smart cards may require certain libraries in order to access their certificates. These libraries must be visible to the NSS library, which spice-gtk uses to provide the smart card to the guest. NSS expects the libraries to provide the PKCS #11 interface.
- Make sure that the module architecture matches spice-gtk/remote-viewer's architecture. For instance, if you have only the 32b PKCS #11 library available, you must install the 32b build of virt-viewer in order for smart cards to work.
Procedure 5.22. Configuring RHEL clients with CoolKey Smart Card Middleware
- CoolKey Smart Card middleware is a part of Red Hat Enterprise Linux. Install the
Smart card supportgroup. If the Smart Card Support group is installed on a Red Hat Enterprise Linux system, smart cards are redirected to the guest when Smart Cards are enabled. The following command installs theSmart card supportgroup:# yum groupinstall "Smart card support"
Procedure 5.23. Configuring RHEL clients with Other Smart Card Middleware
- Register the library in the system's NSS database. Run the following command as root:
# modutil -dbdir /etc/pki/nssdb -add "module name" -libfile /path/to/library.so
Procedure 5.24. Configuring Windows Clients
- Red Hat does not provide PKCS #11 support to Windows clients. Libraries that provide PKCS #11 support must be obtained from third parties. When such libraries are obtained, register them by running the following command as a user with elevated privileges:
modutil -dbdir %PROGRAMDATA%\pki\nssdb -add "module name" -libfile C:\Path\to\module.dll
Chapter 6. Administrative Tasks
6.1. Shutting Down a Virtual Machine
Procedure 6.1. Shutting Down a Virtual Machine
- Click the Virtual Machines tab and select a running virtual machine.
- Click the shut down (
 ) button.Alternatively, right-click the virtual machine and select Shutdown.
) button.Alternatively, right-click the virtual machine and select Shutdown. - Optionally in the Administration Portal, enter a Reason for shutting down the virtual machine in the Shut down Virtual Machine(s) confirmation window. This allows you to provide an explanation for the shutdown, which will appear in the logs and when the virtual machine is powered on again.
Note
The virtual machine shutdown Reason field will only appear if it has been enabled in the cluster settings. For more information, see Explanation of Settings and Controls in the New Cluster and Edit Cluster Windows in the Administration Guide. - Click in the Shut down Virtual Machine(s) confirmation window.
Down.6.2. Suspending a Virtual Machine
Procedure 6.2. Suspending a Virtual Machine
- Click the Virtual Machines tab and select a running virtual machine.
- Click the Suspend (
 ) button.Alternatively, right-click the virtual machine and select Suspend.
) button.Alternatively, right-click the virtual machine and select Suspend.
Suspended.6.3. Rebooting a Virtual Machine
Procedure 6.3. Rebooting a Virtual Machine
- Click the Virtual Machines tab and select a running virtual machine.
- Click the Reboot (
 ) button.Alternatively, right-click the virtual machine and select Reboot.
) button.Alternatively, right-click the virtual machine and select Reboot. - Click in the Reboot Virtual Machine(s) confirmation window.
Reboot In Progress before returning to Up.6.4. Removing a Virtual Machine
Important
Procedure 6.4. Removing Virtual Machines
- Click the Virtual Machines tab and select the virtual machine to remove.
- Click .
- Optionally, select the Remove Disk(s) check box to remove the virtual disks attached to the virtual machine together with the virtual machine. If the Remove Disk(s) check box is cleared, then the virtual disks remain in the environment as floating disks.
- Click .
6.5. Cloning a Virtual Machine
Important
Procedure 6.5. Cloning Virtual Machines
- Click the Virtual Machines tab and select the virtual machine to clone.
- Click .
- Enter a Clone Name for the new virtual machine.
- Click .
6.6. Updating Virtual Machine Guest Agents and Drivers
6.6.1. Updating the Guest Agents and Drivers on Red Hat Enterprise Linux
Procedure 6.6. Updating the Guest Agents and Drivers on Red Hat Enterprise Linux
- Log in to the Red Hat Enterprise Linux virtual machine.
- Update the rhevm-guest-agent-common package:
# yum update rhevm-guest-agent-common
- Restart the service:
- For Red Hat Enterprise Linux 6
# service ovirt-guest-agent restart
- For Red Hat Enterprise Linux 7
# systemctl restart ovirt-guest-agent.service
6.6.2. Updating the Guest Agents and Drivers on Windows
Procedure 6.7. Updating the Guest Agents and Drivers on Windows
- On the Red Hat Virtualization Manager, update the Red Hat Virtualization Guest Tools to the latest version:
# yum update -y rhev-guest-tools-iso*
- Upload the ISO file to your ISO domain, replacing [ISODomain] with the name of your ISO domain:
engine-iso-uploader --iso-domain=[ISODomain] upload /usr/share/rhev-guest-tools-iso/rhev-tools-setup.iso
Note
Therhev-tools-setup.isofile is a symbolic link to the most recently updated ISO file. The link is automatically changed to point to the newest ISO file every time you update the rhev-guest-tools-iso package. - In the Administration or User Portal, if the virtual machine is running, use the Change CD button to attach the latest
rhev-tools-setup.isofile to each of your virtual machines. If the virtual machine is powered off, click the Run Once button and attach the ISO as a CD. - Select the CD Drive containing the updated ISO and execute the
RHEV-ToolsSetup.exefile.
6.7. Viewing Red Hat Satellite Errata for a Virtual Machine
Procedure 6.8. Viewing Red Hat Satellite Errata
- Click the Virtual Machines tab and select a virtual machine.
- Click tab in the details pane.
6.8. Virtual Machines and Permissions
6.8.1. Managing System Permissions for a Virtual Machine
- Create, edit, and remove virtual machines.
- Run, suspend, shutdown, and stop virtual machines.
Note
6.8.2. Virtual Machines Administrator Roles Explained
Table 6.1. Red Hat Virtualization System Administrator Roles
| Role | Privileges | Notes |
|---|---|---|
| DataCenterAdmin | Data Center Administrator | Possesses administrative permissions for all objects underneath a specific data center except for storage. |
| ClusterAdmin | Cluster Administrator | Possesses administrative permissions for all objects underneath a specific cluster. |
| NetworkAdmin | Network Administrator | Possesses administrative permissions for all operations on a specific logical network. Can configure and manage networks attached to virtual machines. To configure port mirroring on a virtual machine network, apply the NetworkAdmin role on the network and the UserVmManager role on the virtual machine. |
6.8.3. Virtual Machine User Roles Explained
Table 6.2. Red Hat Virtualization System User Roles
| Role | Privileges | Notes |
|---|---|---|
| UserRole | Can access and use virtual machines and pools. | Can log in to the User Portal and use virtual machines and pools. |
| PowerUserRole | Can create and manage virtual machines and templates. | Apply this role to a user for the whole environment with the Configure window, or for specific data centers or clusters. For example, if a PowerUserRole is applied on a data center level, the PowerUser can create virtual machines and templates in the data center. Having a PowerUserRole is equivalent to having the VmCreator, DiskCreator, and TemplateCreator roles. |
| UserVmManager | System administrator of a virtual machine. | Can manage virtual machines and create and use snapshots. A user who creates a virtual machine in the User Portal is automatically assigned the UserVmManager role on the machine. |
| UserTemplateBasedVm | Limited privileges to only use Templates. | Level of privilege to create a virtual machine by means of a template. |
| VmCreator | Can create virtual machines in the User Portal. | This role is not applied to a specific virtual machine; apply this role to a user for the whole environment with the Configure window. When applying this role to a cluster, you must also apply the DiskCreator role on an entire data center, or on specific storage domains. |
| VnicProfileUser | Logical network and network interface user for virtual machines. | If the Allow all users to use this Network option was selected when a logical network is created, VnicProfileUser permissions are assigned to all users for the logical network. Users can then attach or detach virtual machine network interfaces to or from the logical network. |
6.8.4. Assigning Virtual Machines to Users
- A User can connect to and use virtual machines. This role is suitable for desktop end users performing day-to-day tasks.
- A PowerUser can create virtual machines and view virtual resources. This role is suitable if you are an administrator or manager who needs to provide virtual resources for your employees.
- A UserVmManager can edit and remove virtual machines, assign user permissions, use snapshots and use templates. It is suitable if you need to make configuration changes to your virtual environment.
Procedure 6.9. Assigning Permissions to Users
- Click the Virtual Machines tab and select a virtual machine.
- Click the Permissions tab on the details pane.
- Click .
- Enter a name, or user name, or part thereof in the Search text box, and click . A list of possible matches display in the results list.
- Select the check box of the user to be assigned the permissions.
- Select UserRole from the Role to Assign drop-down list.
- Click .
Note
6.8.5. Removing Access to Virtual Machines from Users
Procedure 6.10. Removing Access to Virtual Machines from Users
- Click the Virtual Machines tab and select a virtual machine.
- Click the Permissions tab on the details pane.
- Click . A warning message displays, asking you to confirm removal of the selected permissions.
- To proceed, click . To abort, click .
6.9. Snapshots
6.9.1. Creating a Snapshot of a Virtual Machine
Procedure 6.11. Creating a Snapshot of a Virtual Machine
- Click the Virtual Machines tab and select a virtual machine.
- Click the Snapshots tab in the details pane and click .
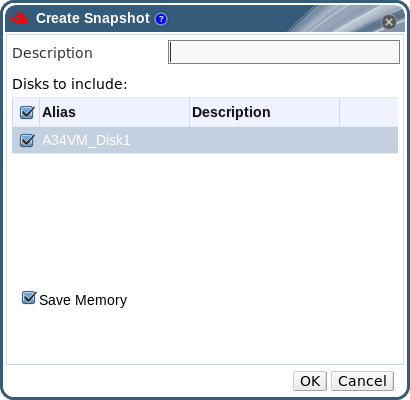
Figure 6.1. Create snapshot
- Enter a description for the snapshot.
- Select Disks to include using the check boxes.
- Use the Save Memory check box to denote whether to include the virtual machine's memory in the snapshot.
- Click .
Locked, which changes to Ok. When you click on the snapshot, its details are shown on the General, Disks, Network Interfaces, and Installed Applications tabs in the right side-pane of the details pane.6.9.2. Using a Snapshot to Restore a Virtual Machine
Procedure 6.12. Using Snapshots to Restore Virtual Machines
- Click the Virtual Machines tab and select a virtual machine.
- Click the Snapshots tab in the details pane to list the available snapshots.
- Select a snapshot to restore in the left side-pane. The snapshot details display in the right side-pane.
- Click the drop-down menu beside to open the Custom Preview Snapshot window.

Figure 6.2. Custom Preview Snapshot
- Use the check boxes to select the VM Configuration, Memory, and disk(s) you want to restore, then click . This allows you to create and restore from a customized snapshot using the configuration and disk(s) from multiple snapshots.The status of the snapshot changes to
Preview Mode. The status of the virtual machine briefly changes toImage Lockedbefore returning toDown. - Start the virtual machine; it runs using the disk image of the snapshot.
- Click Commit to permanently restore the virtual machine to the condition of the snapshot. Any subsequent snapshots are erased.Alternatively, click the Undo button to deactivate the snapshot and return the virtual machine to its previous state.
6.9.3. Creating a Virtual Machine from a Snapshot
Procedure 6.13. Creating a virtual machine from a snapshot
- Click the Virtual Machines tab and select a virtual machine.
- Click the Snapshots tab in the details pane to list the available snapshots.
- Select a snapshot in the list displayed and click .
- Enter the Name and Description for the virtual machine.
- Click .
Image Locked. The virtual machine will remain in this state until Red Hat Virtualization completes the creation of the virtual machine. A virtual machine with a preallocated 20 GB hard drive takes about fifteen minutes to create. Sparsely-allocated virtual disks take less time to create than do preallocated virtual disks.Image Locked to Down in the Virtual Machines tab in the navigation pane.6.9.4. Deleting a Snapshot
Important
- If the snapshot being deleted is contained in a RAW (preallocated) base image, a new volume is created that is the same size as the base image.
- If the snapshot being deleted is contained in a QCOW2 (thin provisioned) base image, the volume subsequent to the volume containing the snapshot being deleted is extended to the cumulative size of the successor volume and the base volume.
- If the snapshot being deleted is contained in a QCOW2 (thin provisioned), non-base image hosted on internal storage, the successor volume is extended to the cumulative size of the successor volume and the volume containing the snapshot being deleted.
6.10. Host Devices
6.10.1. Adding a Host Device to a Virtual Machine
Procedure 6.15. Adding Host Devices to a Virtual Machine
- Select a virtual machine and click the Host Devices tab in the details pane to list the host devices already attached to this virtual machine. A virtual machine can only have devices attached from the same host. If a virtual machine has attached devices from one host, and you attach a device from another host, the attached devices from the previous host will be automatically removed.Attaching host devices to a virtual machine requires the virtual machine to be in a
Downstate. If the virtual machine is running, the changes will not take effect until after the virtual machine has been shut down. - Click to open the Add Host Devices window.
- Use the Pinned Host dropdown menu to select a host.
- Use the Capability dropdown menu to list the
pci,scsi, orusb_devicehost devices. - Select the check boxes of the devices to attach to the virtual machine from the Available Host Devices pane and click the directional arrow button to transfer these devices to the Host Devices to be attached pane, creating a list of the devices to attach to the virtual machine.
- When you have transferred all desired host devices to the Host Devices to be attached pane, click to attach these devices to the virtual machine and close the window.
6.10.2. Removing Host Devices from a Virtual Machine
Procedure 6.16. Removing a Host Device from a Virtual Machine
- Select the virtual machine and click the Host Devices tab in the details pane to list the host devices attached to the virtual machine.
- Select the host device to detach from the virtual machine, or hold Ctrl to select multiple devices, and click to open the Remove Host Device(s) window.
- Click to confirm and detach these devices from the virtual machine.
6.10.3. Pinning a Virtual Machine to Another Host
Procedure 6.17. Pinning a Virtual Machine to a Host
- Select a virtual machine and click the Host Devices tab in the details pane.
- Click to open the Pin VM to Host window.
- Use the Host drop-down menu to select a host.
- Click to pin the virtual machine to the selected host.
6.11. Affinity Groups
Note
Important
VmAffinityGroups filter module or weights module is enabled in the scheduling policy applied to clusters in which affinity groups are defined. The VmAffinityGroups filter module is used to implement hard enforcement, and the VmAffinityGroups weights module is used to implement soft enforcement.6.11.1. Creating an Affinity Group
Procedure 6.18. Creating Affinity Groups
- Click the Virtual Machines tab and select a virtual machine.
- Click the Affinity Groups tab in the details pane.
- Click .
- Enter a Name and Description for the affinity group.
- Select the Positive check box to apply positive affinity, or ensure this check box is cleared to apply negative affinity.
- Select the Enforcing check box to apply hard enforcement, or ensure this check box is cleared to apply soft enforcement.
- Use the drop-down list to select the virtual machines to be added to the affinity group. Use the and buttons to add or remove additional virtual machines.
- Click .
6.11.2. Editing an Affinity Group
Procedure 6.19. Editing Affinity Groups
- Click the Virtual Machines tab and select a virtual machine.
- Click the Affinity Groups tab in the details pane.
- Click .
- Change the Positive and Enforcing check boxes to the preferred values and use the and buttons to add or remove virtual machines to or from the affinity group.
- Click .
6.11.3. Removing an Affinity Group
Procedure 6.20. Removing Affinity Groups
- Click the Virtual Machines tab and select a virtual machine.
- Click the Affinity Groups tab in the details pane.
- Click .
- Click .
6.12. Exporting and Importing Virtual Machines and Templates
Note
- Export the virtual machine or template to an export domain.
- Detach the export domain from one data center, and attach it to another. You can attach it to a different data center in the same Red Hat Virtualization environment, or attach it to a data center in a separate Red Hat Virtualization environment that is managed by another installation of the Red Hat Virtualization Manager.
Note
An export domain can only be active in one data center at a given time. This means that the export domain must be attached to either the source data center or the destination data center. - Import the virtual machine or template into the data center to which the export domain is attached.
Important
6.12.1. Graphical Overview for Exporting and Importing Virtual Machines and Templates
Procedure 6.21. Exporting and Importing Virtual Machines and Templates
- Attach the export domain to the source data center.
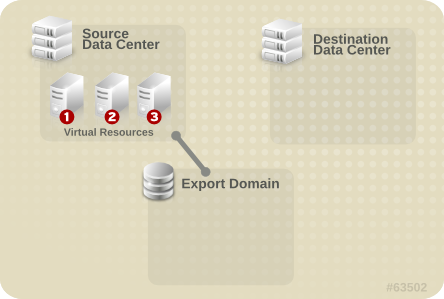
Figure 6.6. Attach Export Domain
- Export the virtual machine or template to the export domain.
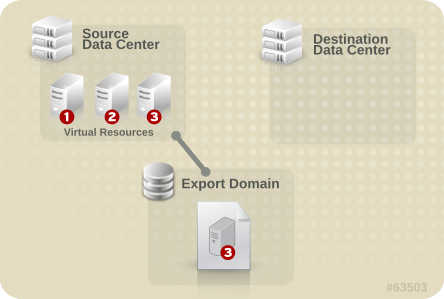
Figure 6.7. Export the Virtual Resource
- Detach the export domain from the source data center.
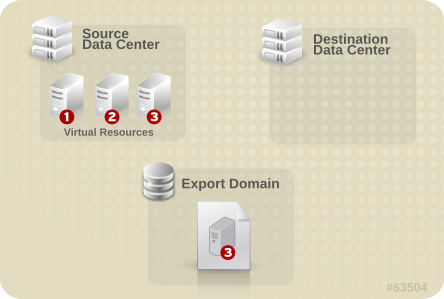
Figure 6.8. Detach Export Domain
- Attach the export domain to the destination data center.
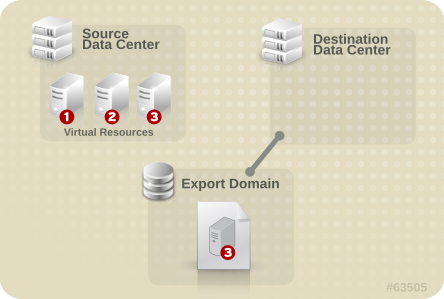
Figure 6.9. Attach the Export Domain
- Import the virtual machine or template into the destination data center.
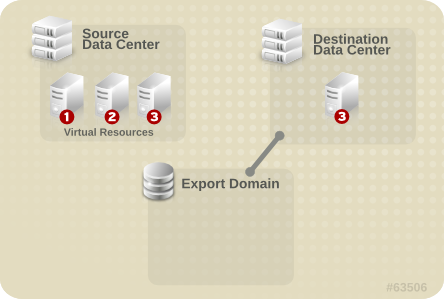
Figure 6.10. Import the virtual resource
6.12.2. Exporting a Virtual Machine to the Export Domain
Warning
Procedure 6.22. Exporting a Virtual Machine to the Export Domain
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Optionally select the following check boxes:
- Force Override: overrides existing images of the virtual machine on the export domain.
- Collapse Snapshots: creates a single export volume per disk. This option removes snapshot restore points and includes the template in a template-based virtual machine, and removes any dependencies a virtual machine has on a template. For a virtual machine that is dependent on a template, either select this option, export the template with the virtual machine, or make sure the template exists in the destination data center.
Note
When you create a virtual machine from a template, two storage allocation options are available under → → .- If Clone was selected, the virtual machine is not dependent on the template. The template does not have to exist in the destination data center.
- If Thin was selected, the virtual machine is dependent on the template, so the template must exist in the destination data center or be exported with the virtual machine. Alternatively, select the Collapse Snapshots check box to collapse the template disk and virtual disk into a single disk.
To check which option was selected, select a virtual machine and click the General tab in the details pane.
- Click .
Image Locked status while it is exported. Depending on the size of your virtual machine hard disk images, and your storage hardware, this can take up to an hour. Use the Events tab to view the progress. When complete, the virtual machine has been exported to the export domain and displays on the VM Import tab of the export domain's details pane.6.12.3. Importing a Virtual Machine into the Destination Data Center
Procedure 6.23. Importing a Virtual Machine into the Destination Data Center
- Click the Storage tab, and select the export domain in the results list. The export domain must have a status of
Active. - Select the VM Import tab in the details pane to list the available virtual machines to import.
- Select one or more virtual machines to import and click .
- Select the Default Storage Domain and Cluster.
- Select the Collapse Snapshots check box to remove snapshot restore points and include templates in template-based virtual machines.
- Click the virtual machine to be imported and click on the Disks sub-tab. From this tab, you can use the Allocation Policy and Storage Domain drop-down lists to select whether the disk used by the virtual machine will be thinly provisioned or preallocated, and can also select the storage domain on which the disk will be stored. An icon is also displayed to indicate which of the disks to be imported acts as the boot disk for that virtual machine.
- Click to import the virtual machines.The Import Virtual Machine Conflict window opens if the virtual machine exists in the virtualized environment.
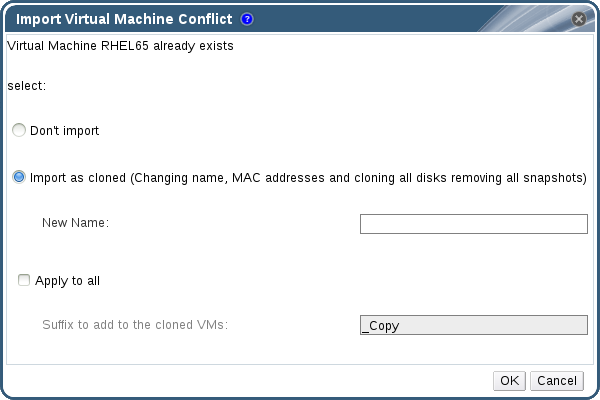
Figure 6.12. Import Virtual Machine Conflict Window
- Choose one of the following radio buttons:
- Don't import
- Import as cloned and enter a unique name for the virtual machine in the New Name field.
- Optionally select the Apply to all check box to import all duplicated virtual machines with the same suffix, and then enter a suffix in the Suffix to add to the cloned VMs field.
- Click OK.
Important
6.12.4. Importing a Virtual Machine from a VMware Provider
Warning
Procedure 6.24. Importing a Virtual Machine from VMware
- In the Virtual Machines tab, click to open the Import Virtual Machine(s) window.
- Select VMware from the Source list.
- If you have configured a VMware provider as an external provider, select it from the External Provider list. Verify that the provider credentials are correct. If you did not specify a destination data center or proxy host when configuring the external provider, select those options now.
- If you have not configured a VMware provider, or want to import from a new VMware provider, provide the following details:
- Select from the list the Data Center in which the virtual machine will be available.
- Enter the IP address or fully qualified domain name of the VMware vCenter instance in the vCenter field.
- Enter the IP address or fully qualified domain name of the host from which the virtual machines will be imported in the ESXi field.
- Enter the name of the data center and the cluster in which the specified ESXi host resides in the Data Center field.
- If you have exchanged the SSL certificate between the ESXi host and the Manager, leave Verify server's SSL certificate checked to verify the ESXi host's certificate. If not, uncheck the option.
- Enter the Username and Password for the VMware vCenter instance. The user must have access to the VMware data center and ESXi host on which the virtual machines reside.
- Select a host in the chosen data center with virt-v2v installed to serve as the Proxy Host during virtual machine import operations. This host must also be able to connect to the network of the VMware vCenter external provider.
- Click to generate a list of the virtual machines on the VMware provider.
- Select one or more virtual machines from the Virtual Machines on Source list, and use the arrows to move them to the Virtual Machines to Import list. Click .
Important
An import operation can only include virtual machines that share the same architecture. If any virtual machine to be imported has a different architecture, a warning will display and you will be prompted to change your selection to include only virtual machines with the same architecture.Note
If a virtual machine's network device uses the driver type e1000 or rtl8139, the virtual machine will use the same driver type after it has been imported to Red Hat Virtualization.If required, you can change the driver type to VirtIO manually after the import. To change the driver type after a virtual machine has been imported, see Section 5.3.2, “Editing a Network Interface”. If the network device uses driver types other than e1000 or rtl8139, the driver type is changed to VirtIO automatically during the import. The Attach VirtIO-drivers option allows the VirtIO drivers to be injected to the imported virtual machine files so that when the driver is changed to VirtIO, the device will be properly detected by the operating system. - Select the Cluster in which the virtual machines will reside.
- Select a CPU Profile for the virtual machines.
- Select the Collapse Snapshots check box to remove snapshot restore points and include templates in template-based virtual machines.
- Select the Clone check box to change the virtual machine name and MAC addresses, and clone all disks, removing all snapshots. If a virtual machine appears with a warning symbol beside its name or has a tick in the VM in System column, you must clone the virtual machine and change its name.
- Click on each virtual machine to be imported and click on the Disks sub-tab. Use the Allocation Policy and Storage Domain lists to select whether the disk used by the virtual machine will be thinly provisioned or preallocated, and select the storage domain on which the disk will be stored. An icon is also displayed to indicate which of the disks to be imported acts as the boot disk for that virtual machine.
Note
The target storage domain must be a filed-based domain. Due to current limitations, specifying a block-based domain causes the V2V operation to fail. - If you selected the Clone check box, change the name of the virtual machine in the General sub-tab.
- Click to import the virtual machines.
6.12.5. Importing an OVA File from VMware
Important
Procedure 6.25. Importing an OVA File
- Copy the OVA file to a host in your cluster, in a file system location such as
/var/tmp.Note
The location can be a local directory or a remote nfs mount, as long as it has sufficient space and is accessible to theqemuuser (UID 36). - Ensure that the OVA file has permissions allowing read/write access to the
qemuuser (UID 36) and thekvmgroup (GID 36):# chown 36:36 path_to_OVA_file/file.OVA
- In the Virtual Machines tab, click to open the Import Virtual Machine(s) window.
- Select VMware Virtual Appliance (OVA) from the Source list.
- Select a host from the Host list. This will be the same host that you exported from the VMware provider.
- In the Path box, specify the path of the OVA file.
- Click to list the virtual machines that can be imported.
- Select one or more virtual machines from the Virtual Machines on Source list, and use the arrows to move them to the Virtual Machines to Import list. Click .
- Select the Target Cluster where the virtual machines will reside.
- Select the CPU Profile for the virtual machines.
- Select the Allocation Policy for the virtual machines.
- Optionally, select the Attach VirtIO-Drivers check box and select the appropriate image on the list to add VirtIO drivers.
- Select the Allocation Policy for the virtual machines.
- Click each virtual machine you will be importing. On the General sub-tab, select the Operating System.
- On the Network Interfaces sub-tab, select the Network Name and Profile Name.
- Click the Disks sub-tab to view the Alias, Virtual Size and Actual Size of the virtual machine.
- Click to import the virtual machines.
6.12.6. Importing a Virtual Machine from a Xen Host
Warning
Procedure 6.26. Importing a Virtual Machine from Xen
- Enable public key authentication between the V2V host and the Xen host:
- Log in to the V2V host and generate SSH keys for the
vdsmuser.# sudo -u vdsm ssh-keygen
- Copy the
vdsmuser's public key to the Xen host.# sudo -u vdsm ssh-copy-id root@xenhost.example.com
- Log in to the Xen host to add it to the V2V host's
known_hostsfile.# sudo -u vdsm ssh root@xenhost.example.com
- Log in to the Administration Portal. In the Virtual Machines tab, click to open the Import Virtual Machine(s) window.
- Select the Data Center that contains the V2V host.
- Select XEN (via RHEL) from the Source drop-down list.
- Enter the URI of the Xen host. The required format is pre-filled; you must replace
<hostname>with the host name of the Xen host. - Select the V2V host from the Proxy Host drop-down list.
- Click to generate a list of the virtual machines on the Xen host.
- Select one or more virtual machines from the Virtual Machines on Source list, and use the arrows to move them to the Virtual Machines to Import list.
Note
Due to current limitations, Xen virtual machines with block devices do not appear in the Virtual Machines on Source list, and cannot be imported to Red Hat Virtualization. - Click .
Important
An import operation can only include virtual machines that share the same architecture. If any virtual machine to be imported has a different architecture, a warning will display and you will be prompted to change your selection to include only virtual machines with the same architecture. - Select the Cluster in which the virtual machines will reside.
- Select a CPU Profile for the virtual machines.
- Select the Collapse Snapshots check box to remove snapshot restore points and include templates in template-based virtual machines.
- Select the Clone check box to change the virtual machine name and MAC addresses, and clone all disks, removing all snapshots. If a virtual machine appears with a warning symbol beside its name or has a tick in the VM in System column, you must clone the virtual machine and change its name.
- Click on each virtual machine to be imported and click on the Disks sub-tab. Use the Allocation Policy and Storage Domain lists to select whether the disk used by the virtual machine will be thinly provisioned or preallocated, and select the storage domain on which the disk will be stored. An icon is also displayed to indicate which of the disks to be imported acts as the boot disk for that virtual machine.
Note
The target storage domain must be a filed-based domain. Due to current limitations, specifying a block-based domain causes the V2V operation to fail. - If you selected the Clone check box, change the name of the virtual machine in the General sub-tab.
- Click to import the virtual machines.
6.12.7. Importing a Virtual Machine from a KVM Host
Warning
Procedure 6.27. Importing a Virtual Machine from KVM
- Enable public key authentication between the proxy host and the KVM host:
- Log in to the proxy host and generate SSH keys for the
vdsmuser.# sudo -u vdsm ssh-keygen
- Copy the
vdsmuser's public key to the KVM host.# sudo -u vdsm ssh-copy-id root@kvmhost.example.com
- Log in to the KVM host to add it to the proxy host's
known_hostsfile.# sudo -u vdsm ssh root@kvmhost.example.com
- Log in to the Administration Portal. In the Virtual Machines tab, click to open the Import Virtual Machine(s) window.
- Select the Data Center that contains the proxy host.
- Select KVM (via Libvirt) from the Source drop-down list.
- Enter the URI of the KVM host in the following format:
qemu+ssh://root@kvmhost.example.com/system
- Keep the Requires Authentication check box selected.
- Enter
rootin the Username field. - Enter the Password of the KVM host's root user.
- Select the Proxy Host from the drop-down list.
- Click to generate a list of the virtual machines on the KVM host.
- Select one or more virtual machines from the Virtual Machines on Source list, and use the arrows to move them to the Virtual Machines to Import list.
- Click .
Important
An import operation can only include virtual machines that share the same architecture. If any virtual machine to be imported has a different architecture, a warning will display and you will be prompted to change your selection to include only virtual machines with the same architecture. - Select the Cluster in which the virtual machines will reside.
- Select a CPU Profile for the virtual machines.
- Select the Collapse Snapshots check box to remove snapshot restore points and include templates in template-based virtual machines.
- Select the Clone check box to change the virtual machine name and MAC addresses, and clone all disks, removing all snapshots. If a virtual machine appears with a warning symbol beside its name or has a tick in the VM in System column, you must clone the virtual machine and change its name.
- Click on each virtual machine to be imported and click on the Disks sub-tab. Use the Allocation Policy and Storage Domain lists to select whether the disk used by the virtual machine will be thinly provisioned or preallocated, and select the storage domain on which the disk will be stored. An icon is also displayed to indicate which of the disks to be imported acts as the boot disk for that virtual machine.
Note
The target storage domain must be a filed-based domain. Due to current limitations, specifying a block-based domain causes the operation to fail. - If you selected the Clone check box, change the name of the virtual machine in the General sub-tab.
- Click to import the virtual machines.
6.13. Migrating Virtual Machines Between Hosts
6.13.1. Live Migration Prerequisites
- The source and destination host should both be members of the same cluster, ensuring CPU compatibility between them.
Note
Live migrating virtual machines between different clusters is generally not recommended. The currently only supported use case is documented at https://access.redhat.com/articles/1390733. - The source and destination host must have a status of
Up. - The source and destination host must have access to the same virtual networks and VLANs.
- The source and destination host must have access to the data storage domain on which the virtual machine resides.
- There must be enough CPU capacity on the destination host to support the virtual machine's requirements.
- There must be enough RAM on the destination host that is not in use to support the virtual machine's requirements.
- The migrating virtual machine must not have the
cache!=nonecustom property set.
6.13.2. Optimizing Live Migration
Procedure 6.28. Configuring Auto-convergence and Migration Compression for Virtual Machine Migration
- Configure the optimization settings at the global level:
- Enable auto-convergence at the global level:
# engine-config -s DefaultAutoConvergence=True
- Enable migration compression at the global level:
# engine-config -s DefaultMigrationCompression=True
- Restart the
ovirt-engineservice to apply the changes:# systemctl restart ovirt-engine.service
- Configure the optimization settings at the cluster level:
- Select a cluster.
- Click .
- Click the Migration Policy tab.
- From the Auto Converge migrations list, select Inherit from global setting, Auto Converge, or Don't Auto Converge.
- From the Enable migration compression list, select Inherit from global setting, Compress, or Don't Compress.
- Configure the optimization settings at the virtual machine level:
- Select a virtual machine.
- Click .
- Click the Host tab.
- From the Auto Converge migrations list, select Inherit from cluster setting, Auto Converge, or Don't Auto Converge.
- From the Enable migration compression list, select Inherit from cluster setting, Compress, or Don't Compress.
6.13.3. Guest Agent Hooks
- Before migration
- After migration
- Before hibernation
- After hibernation
/etc/ovirt-guest-agent/hooks.d on Linux systems and C:\Program Files\Redhat\RHEV\Drivers\Agent on Windows systems.before_migration and after_migration, before_hibernation and after_hibernation. All files or symbolic links in that directory will be executed.ovirtagent. If the script needs root permissions, the elevation must be executed by the creator of the hook script.System Service user.6.13.4. Automatic Virtual Machine Migration
6.13.5. Preventing Automatic Migration of a Virtual Machine
Procedure 6.29. Preventing Automatic Migration of Virtual Machine
- Click the Virtual Machines tab and select a virtual machine.
- Click Edit.
- Click the Host tab.
- Use the Start Running On radio buttons to designate the virtual machine to run on Any Host in Cluster or a Specific host. If applicable, select a specific host or group of hosts from the list.
Warning
Explicitly assigning a virtual machine to one specific host and disabling migration is mutually exclusive with Red Hat Virtualization high availability. Virtual machines that are assigned to one specific host can only be made highly available using third party high availability products like Red Hat High Availability. This restriction does not apply to virtual machines that are assigned to multiple specific hosts.Important
If the virtual machine has host devices directly attached to it, and a different host is specified, the host devices from the previous host will be automatically removed from the virtual machine. - Select Allow manual migration only or Do not allow migration from the Migration Options drop-down list.
- Optionally, select the Use custom migration downtime check box and specify a value in milliseconds.
- Click .
6.13.6. Manually Migrating Virtual Machines
Note
Note
Procedure 6.30. Manually Migrating Virtual Machines
- Click the Virtual Machines tab and select a running virtual machine.
- Click .
- Use the radio buttons to select whether to Select Host Automatically or to Select Destination Host, specifying the host using the drop-down list.
Note
When the Select Host Automatically option is selected, the system determines the host to which the virtual machine is migrated according to the load balancing and power management rules set up in the scheduling policy. - Click .
6.13.7. Setting Migration Priority
Procedure 6.31. Setting Migration Priority
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Select the High Availability tab.
- Select Low, Medium, or High from the Priority drop-down list.
- Click .
6.13.8. Canceling Ongoing Virtual Machine Migrations
Procedure 6.32. Canceling Ongoing Virtual Machine Migrations
- Select the migrating virtual machine. It is displayed in the Virtual Machines resource tab with a status of Migrating from.
- Click .
6.13.9. Event and Log Notification upon Automatic Migration of Highly Available Virtual Servers
Example 6.1. Notification in the Events Tab of the Web Admin Portal
Example 6.2. Notification in the Manager engine.log
/var/log/ovirt-engine/engine.log:6.14. Improving Uptime with Virtual Machine High Availability
6.14.1. What is High Availability?
6.14.2. Why Use High Availability?
- When a host becomes non-operational due to hardware failure.
- When a host is put into maintenance mode for scheduled downtime.
- When a host becomes unavailable because it has lost communication with an external storage resource.
6.14.3. High Availability Considerations
- Power management must be configured for the hosts running the highly available virtual machines.
- The host running the highly available virtual machine must be part of a cluster which has other available hosts.
- The destination host must be running.
- The source and destination host must have access to the data domain on which the virtual machine resides.
- The source and destination host must have access to the same virtual networks and VLANs.
- There must be enough CPUs on the destination host that are not in use to support the virtual machine's requirements.
- There must be enough RAM on the destination host that is not in use to support the virtual machine's requirements.
6.14.4. Configuring a Highly Available Virtual Machine
Procedure 6.33. Configuring a Highly Available Virtual Machine
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Click the High Availability tab.
- Select the Highly Available check box to enable high availability for the virtual machine.
- Select Low, Medium, or High from the Priority drop-down list. When migration is triggered, a queue is created in which the high priority virtual machines are migrated first. If a cluster is running low on resources, only the high priority virtual machines are migrated.
- Click .
6.15. Other Virtual Machine Tasks
6.15.1. Enabling SAP Monitoring
Procedure 6.34. Enabling SAP Monitoring on Virtual Machines
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Click the Custom Properties tab.
- Select
sap_agentfrom the drop-down list. Ensure the secondary drop-down menu is set to True.If previous properties have been set, select the plus sign to add a new property rule and selectsap_agent. - Click .
6.15.2. Configuring Red Hat Enterprise Linux 5.4 and Higher Virtual Machines to use SPICE
Note
6.15.2.1. Installing and Configuring QXL Drivers
Procedure 6.35. Installing QXL Drivers
- Log in to a Red Hat Enterprise Linux virtual machine.
- Install the QXL drivers:
# yum install xorg-x11-drv-qxl
Procedure 6.36. Configuring QXL drivers in GNOME
- Click System.
- Click Administration.
- Click Display.
- Click the Hardware tab.
- Click Video Cards Configure.
- Select qxl and click OK.
- Restart X-Windows by logging out of the virtual machine and logging back in.
Procedure 6.37. Configuring QXL drivers on the command line:
- Back up
/etc/X11/xorg.conf:# cp /etc/X11/xorg.conf /etc/X11/xorg.conf.$$.backup
- Make the following change to the Device section of
/etc/X11/xorg.conf:Section "Device" Identifier "Videocard0" Driver "qxl" Endsection
6.15.2.2. Configuring a Virtual Machine's Tablet and Mouse to use SPICE
/etc/X11/xorg.conf file to enable SPICE for your virtual machine's tablet devices.Procedure 6.38. Configuring a Virtual Machine's Tablet and Mouse to use SPICE
- Verify that the tablet device is available on your guest:
# /sbin/lsusb -v | grep 'QEMU USB Tablet'
If there is no output from the command, do not continue configuring the tablet. - Back up
/etc/X11/xorg.conf:# cp /etc/X11/xorg.conf /etc/X11/xorg.conf.$$.backup
- Make the following changes to
/etc/X11/xorg.conf:Section "ServerLayout" Identifier "single head configuration" Screen 0 "Screen0" 0 0 InputDevice "Keyboard0" "CoreKeyboard" InputDevice "Tablet" "SendCoreEvents" InputDevice "Mouse" "CorePointer" EndSection Section "InputDevice" Identifier "Mouse" Driver "void" #Option "Device" "/dev/input/mice" #Option "Emulate3Buttons" "yes" EndSection Section "InputDevice" Identifier "Tablet" Driver "evdev" Option "Device" "/dev/input/event2" Option "CorePointer" "true" EndSection
- Log out and log back into the virtual machine to restart X-Windows.
6.15.3. KVM virtual machine timing management
pvclock provides a stable source of timing for KVM guests that support it.- Clocks can fall out of synchronization with the actual time which invalidates sessions and affects networks.
- Virtual machines with slower clocks may have issues migrating.
Important
ntpd service and add it to the default startup sequence:- For Red Hat Enterprise Linux 6
# service ntpd start # chkconfig ntpd on
- For Red Hat Enterprise Linux 7
# systemctl start ntpd.service # systemctl enable ntpd.service
ntpd service should minimize the affects of clock skew in all cases.Your CPU has a constant Time Stamp Counter if the constant_tsc flag is present. To determine if your CPU has the constant_tsc flag run the following command:
$ cat /proc/cpuinfo | grep constant_tsc
constant_tsc bit. If no output is given follow the instructions below.Systems without constant time stamp counters require additional configuration. Power management features interfere with accurate time keeping and must be disabled for virtual machines to accurately keep time with KVM.
Important
constant_tsc bit, disable all power management features (BZ#513138). Each system has several timers it uses to keep time. The TSC is not stable on the host, which is sometimes caused by cpufreq changes, deep C state, or migration to a host with a faster TSC. Deep C sleep states can stop the TSC. To prevent the kernel using deep C states append "processor.max_cstate=1" to the kernel boot options in the grub.conf file on the host:term Red Hat Enterprise Linux Server (2.6.18-159.el5)
root (hd0,0)
kernel /vmlinuz-2.6.18-159.el5 ro root=/dev/VolGroup00/LogVol00 rhgb quiet processor.max_cstate=1cpufreq (only necessary on hosts without the constant_tsc) by editing the /etc/sysconfig/cpuspeed configuration file and change the MIN_SPEED and MAX_SPEED variables to the highest frequency available. Valid limits can be found in the /sys/devices/system/cpu/cpu*/cpufreq/scaling_available_frequencies files.engine-config tool to receive alerts when hosts drift out of sync.You can use the engine-config tool to configure alerts when your hosts drift out of sync.
EnableHostTimeDrift and HostTimeDriftInSec. EnableHostTimeDrift, with a default value of false, can be enabled to receive alert notifications of host time drift. The HostTimeDriftInSec parameter is used to set the maximum allowable drift before alerts start being sent.For certain Red Hat Enterprise Linux virtual machines, additional kernel parameters are required. These parameters can be set by appending them to the end of the /kernel line in the /boot/grub/grub.conf file of the virtual machine.
Note
ktune packagektune package provides an interactive Bourne shell script, fix_clock_drift.sh. When run as the superuser, this script inspects various system parameters to determine if the virtual machine on which it is run is susceptible to clock drift under load. If so, it then creates a new grub.conf.kvm file in the /boot/grub/ directory. This file contains a kernel boot line with additional kernel parameters that allow the kernel to account for and prevent significant clock drift on the KVM virtual machine. After running fix_clock_drift.sh as the superuser, and once the script has created the grub.conf.kvm file, then the virtual machine's current grub.conf file should be backed up manually by the system administrator, the new grub.conf.kvm file should be manually inspected to ensure that it is identical to grub.conf with the exception of the additional boot line parameters, the grub.conf.kvm file should finally be renamed grub.conf, and the virtual machine should be rebooted.| Red Hat Enterprise Linux | Additional virtual machine kernel parameters |
|---|---|
| 5.4 AMD64/Intel 64 with the paravirtualized clock | Additional parameters are not required |
| 5.4 AMD64/Intel 64 without the paravirtualized clock | notsc lpj=n |
| 5.4 x86 with the paravirtualized clock | Additional parameters are not required |
| 5.4 x86 without the paravirtualized clock | clocksource=acpi_pm lpj=n |
| 5.3 AMD64/Intel 64 | notsc |
| 5.3 x86 | clocksource=acpi_pm |
| 4.8 AMD64/Intel 64 | notsc |
| 4.8 x86 | clock=pmtmr |
| 3.9 AMD64/Intel 64 | Additional parameters are not required |
| 3.9 x86 | Additional parameters are not required |
Chapter 7. Templates
7.1. Sealing Virtual Machines in Preparation for Deployment as Templates
7.1.1. Sealing a Linux Virtual Machine for Deployment as a Template
sys-unconfig command. Sealing a Linux virtual machine manually requires you to create a file on the virtual machine that acts as a flag for initiating various configuration tasks the next time you start that virtual machine. The sys-unconfig command allows you to automate this process. However, both of these methods also require you to manually delete files on the virtual machine that are specific to that virtual machine or might cause conflicts amongst virtual machines created based on the template you will create based on that virtual machine. As such, both are valid methods for sealing a Linux virtual machine and will achieve the same result.7.1.1.1. Sealing a Linux Virtual Machine Manually for Deployment as a Template
Procedure 7.1. Sealing a Linux Virtual Machine
- Log in to the virtual machine.
- Flag the system for re-configuration:
- For Red Hat Enterprise Linux (RHEL) 6:
# touch /.unconfigured
- For RHEL 7 or Red Hat Virtualization Host (RHVH) 4.0:
# yum install initial-setup
Note
Your system must be registered to receive theinital-setuppackage.
- Remove the SSH host keys:
# rm -rf /etc/ssh/ssh_host_*
- Change the host name to
localhost.localdomain:- For RHEL 6, edit the
HOSTNAMEvalue in/etc/sysconfig/network:HOSTNAME=localhost.localdomain
- For RHEL 7 or RHVH 4.0, use the
hostnamectlcommand:# hostnamectl set-hostname localhost.localdomain
- Remove
/etc/udev/rules.d/70-*:# rm -rf /etc/udev/rules.d/70-*
- Remove the
HWADDRline andUUIDline from/etc/sysconfig/network-scripts/ifcfg-eth*. Ensure that all static information, such as IP address, DNS, or gateway, is deleted from this file. - Delete
machine-idfrom/etc/machine-id:# cd /etc # chmod 777 machine-id # vi machine-id
Delete themachine id.# chmod 444 machine-id
- For RHEL 7, enable the
initial-setupservice:# systemctl enable initial-setup.service
- Unregister the system:
# subscription-manager unregister # subscription-manager remove --all # subscription-manager clean
- Optionally, delete all the logs from
/var/logand build logs from/root. - Shut down the virtual machine:
# poweroff
7.1.1.2. Sealing a Linux Virtual Machine for Deployment as a Template using sys-unconfig
Procedure 7.2. Sealing a Linux Virtual Machine using sys-unconfig
- Log in to the virtual machine.
- Remove SSH host keys:
# rm -rf /etc/ssh/ssh_host_*
- Change the host name to
localhost.localdomain.- For Red Hat Enterprise Linux 6, edit the
HOSTNAMEvalue in/etc/sysconfig/network:HOSTNAME=localhost.localdomain
- For Red Hat Enterprise Linux 7, use the
hostnamectlcommand:# hostnamectl set-hostname localhost.localdomain
- Remove the
HWADDRline andUUIDline from/etc/sysconfig/network-scripts/ifcfg-eth*. - Optionally, delete all the logs from
/var/logand build logs from/root. - Run the following command:
# sys-unconfig
7.1.2. Sealing a Windows Virtual Machine for Deployment as a Template
/usr/share/ovirt-engine/conf/sysprep/ directory. These files act as templates for Sysprep. The fields in these files can be copied, pasted, and altered as required. This definition will override any values entered into the Initial Run fields of the Edit Virtual Machine window./usr/share/ovirt-engine/conf/sysprep/ directory. For example, "<Domain><![CDATA[$JoinDomain$]]></Domain>" can be used to indicate the domain to join.7.1.2.1. Prerequisites for Sealing a Windows Virtual Machine
Important
- The Windows virtual machine parameters have been correctly defined.
- If not, click Edit the Virtual Machines tab and enter the required information in the Operating System and Cluster fields.
- The correct product key has been defined in an override file on the Manager.The override file must be created under
/etc/ovirt-engine/osinfo.conf.d/, have a filename that puts it after/etc/ovirt-engine/osinfo.conf.d/00-defaults.properties, and ends in.properties. For example,/etc/ovirt-engine/osinfo.conf.d/10-productkeys.properties. The last file will have precedence and override any other previous file.If not, copy the default values for your Windows operating system from/etc/ovirt-engine/osinfo.conf.d/00-defaults.propertiesinto the override file, and input your values in theproductKey.valueandsysprepPath.valuefields.Example 7.1. Windows 7 Default Configuration Values
# Windows7(11, OsType.Windows, false),false os.windows_7.id.value = 11 os.windows_7.name.value = Windows 7 os.windows_7.derivedFrom.value = windows_xp os.windows_7.sysprepPath.value = ${ENGINE_USR}/conf/sysprep/sysprep.w7 os.windows_7.productKey.value = os.windows_7.devices.audio.value = ich6 os.windows_7.devices.diskInterfaces.value.3.3 = IDE, VirtIO_SCSI, VirtIO os.windows_7.devices.diskInterfaces.value.3.4 = IDE, VirtIO_SCSI, VirtIO os.windows_7.devices.diskInterfaces.value.3.5 = IDE, VirtIO_SCSI, VirtIO os.windows_7.isTimezoneTypeInteger.value = false
7.1.2.2. Sealing a Windows 7, Windows 2008, or Windows 2012 Template
Procedure 7.3. Sealing a Windows 7, Windows 2008, or Windows 2012 Template
- Launch Sysprep from
C:\Windows\System32\sysprep\sysprep.exe. - Enter the following information into Sysprep:
- Under System Cleanup Action, select Enter System Out-of-Box-Experience (OOBE).
- Select the Generalize check box if you need to change the computer's system identification number (SID).
- Under Shutdown Options, select Shutdown.
- Click to complete the sealing process; the virtual machine shuts down automatically upon completion.
7.2. Creating a Template
Important
Procedure 7.4. Creating a Template
- Click the Virtual Machines tab and select the source virtual machine.
- Ensure the virtual machine is powered down and has a status of
Down. - Click . For more details on all fields in the New Template window, see Section A.4, “Explanation of Settings in the New Template and Edit Template Windows”.
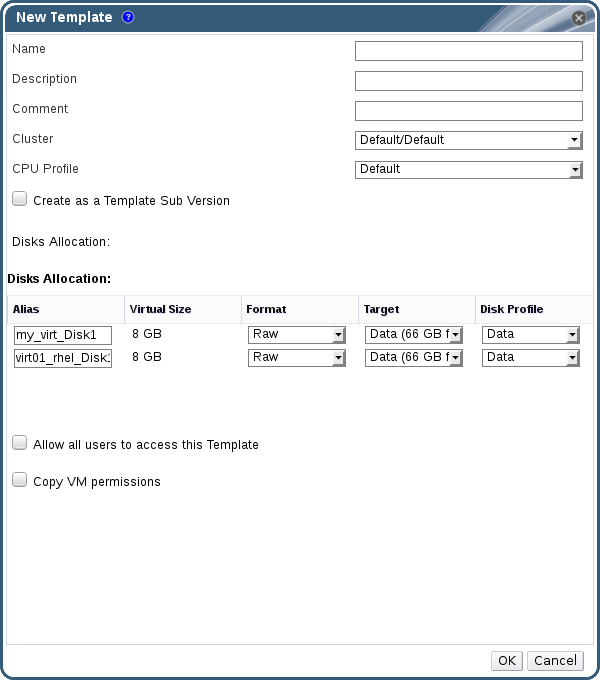
Figure 7.1. The New Template window
- Enter a Name, Description, and Comment for the template.
- Select the cluster with which to associate the template from the Cluster drop-down list. By default, this is the same as that of the source virtual machine.
- Optionally, select a CPU profile for the template from the CPU Profile drop-down list.
- Optionally, select the Create as a Template Sub Version check box, select a Root Template, and enter a Sub Version Name to create the new template as a sub template of an existing template.
- In the Disks Allocation section, enter an alias for the disk in the Alias text field. Select the disk format in the Format drop-down, the storage domain on which to store the disk from the Target drop-down, and the disk profile in the Disk Profile drop-down. By default, these are the same as those of the source virtual machine.
- Select the Allow all users to access this Template check box to make the template public.
- Select the Copy VM permissions check box to copy the permissions of the source virtual machine to the template.
- Click .
Image Locked while the template is being created. The process of creating a template may take up to an hour depending on the size of the virtual disk and the capabilities of your storage hardware. When complete, the template is added to the Templates tab. You can now create new virtual machines based on the template.Note
7.3. Editing a Template
Procedure 7.5. Editing a Template
- Click the Templates tab and select a template.
- Click .
- Change the necessary properties.
- Click .
7.4. Deleting a Template
Procedure 7.6. Deleting a Template
- Click the Templates tab and select a template.
- Click .
- Click .
7.5. Exporting Templates
7.5.1. Migrating Templates to the Export Domain
Note
Procedure 7.7. Exporting Individual Templates to the Export Domain
- Click the Templates tab and select a template.
- Click .
- Select the Force Override check box to replace any earlier version of the template on the export domain.
- Click to begin exporting the template; this may take up to an hour, depending on the virtual disk image size and your storage hardware.
7.5.2. Copying a Template's Virtual Hard Disk
Procedure 7.8. Copying a Virtual Hard Disk
- Click the Disks tab and select the template disk(s) to copy.
- Click Copy.
- Select the Target data domain from the drop-down list(s).
- Click OK.
7.6. Importing Templates
7.6.1. Importing a Template into a Data Center
Note
Procedure 7.9. Importing a Template into a Data Center
- Click the Storage tab and select the newly attached export domain.
- Click the Template Import tab in the details pane and select a template.
- Click .
- Select the templates to import.
- Use the drop-down lists to select the Destination Cluster and Storage domain. Alter the Suffix if applicable.Alternatively, clear the Clone All Templates check box.
- Click to import templates and open a notification window. Click to close the notification window.
7.6.2. Importing a Virtual Disk Image from an OpenStack Image Service as a Template
- Click the Storage tab and select the OpenStack Image Service domain.
- Click the Images tab in the details pane and select the image to import.
- Click .
Note
If you are importing an image from a Glance storage domain, you have the option of specifying the template name. - Select the Data Center into which the virtual disk image will be imported.
- Select the storage domain in which the virtual disk image will be stored from the Domain Name drop-down list.
- Optionally, select a Quota to apply to the virtual disk image.
- Select the Import as Template check box.
- Select the Cluster in which the virtual disk image will be made available as a template.
- Click .
7.7. Templates and Permissions
7.7.2. Template Administrator Roles Explained
Table 7.1. Red Hat Virtualization System Administrator Roles
| Role | Privileges | Notes |
|---|---|---|
| TemplateAdmin | Can perform all operations on templates. | Has privileges to create, delete and configure a template's storage domain and network details, and to move templates between domains. |
| NetworkAdmin | Network Administrator | Can configure and manage networks attached to templates. |
7.7.3. Template User Roles Explained
Table 7.2. Red Hat Virtualization Template User Roles
| Role | Privileges | Notes |
|---|---|---|
| TemplateCreator | Can create, edit, manage and remove virtual machine templates within assigned resources. | The TemplateCreator role is not applied to a specific template; apply this role to a user for the whole environment with the Configure window. Alternatively apply this role for specific data centers, clusters, or storage domains. |
| TemplateOwner | Can edit and delete the template, assign and manage user permissions for the template. | The TemplateOwner role is automatically assigned to the user who creates a template. Other users who do not have TemplateOwner permissions on a template cannot view or use the template. |
| UserTemplateBasedVm | Can use the template to create virtual machines. | Cannot edit template properties. |
| VnicProfileUser | Logical network and network interface user for templates. | If the Allow all users to use this Network option was selected when a logical network is created, VnicProfileUser permissions are assigned to all users for the logical network. Users can then attach or detach template network interfaces to or from the logical network. |
7.7.4. Assigning an Administrator or User Role to a Resource
Procedure 7.10. Assigning a Role to a Resource
- Use the resource tabs, tree mode, or the search function to find and select the resource in the results list.
- Click the tab in the details pane to list the assigned users, the user's role, and the inherited permissions for the selected resource.
- Click .
- Enter the name or user name of an existing user into the Search text box and click . Select a user from the resulting list of possible matches.
- Select a role from the Role to Assign: drop-down list.
- Click .
7.7.5. Removing an Administrator or User Role from a Resource
Procedure 7.11. Removing a Role from a Resource
- Use the resource tabs, tree mode, or the search function to find and select the resource in the results list.
- Click the tab in the details pane to list the assigned users, the user's role, and the inherited permissions for the selected resource.
- Select the user to remove from the resource.
- Click . The Remove Permission window opens to confirm permissions removal.
- Click .
7.8. Using Cloud-Init to Automate the Configuration of Virtual Machines
7.8.1. Cloud-Init Use Case Scenarios
- Virtual Machines Created Based on TemplatesYou can use the Cloud-Init options in the Initial Run section of the Run Once window to initialize a virtual machine that was created based on a template. This allows you to customize the virtual machine the first time that virtual machine is started.
- Virtual Machine TemplatesYou can use the Use Cloud-Init/Sysprep options in the Initial Run tab of the New Template and Edit Template windows to specify options for customizing virtual machines created based on that template.
- Virtual Machine PoolsYou can use the Use Cloud-Init/Sysprep options in the Initial Run tab of the New Pool window to specify options for customizing virtual machines taken from that virtual machine pool. This allows you to specify a set of standard settings that will be applied every time a virtual machine is taken from that virtual machine pool. You can inherit or override the options specified for the template on which the virtual machine is based, or specify options for the virtual machine pool itself.
7.8.2. Installing Cloud-Init
Procedure 7.12. Installing Cloud-Init
- Log on to the virtual machine.
- Enable the required repositories:
- Red Hat Enterprise Linux 6:
# subscription-manager repos --enable=rhel-6-server-rpms # subscription-manager repos --enable=rhel-6-server-rh-common-rpms
- Red Hat Enterprise Linux 7:
# subscription-manager repos --enable=rhel-7-server-rpms # subscription-manager repos --enable=rhel-7-server-rh-common-rpms
- Install the cloud-init package and dependencies:
# yum install cloud-init
7.8.3. Using Cloud-Init to Prepare a Template
Note
Procedure 7.13. Using Cloud-Init to Prepare a Template
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Click the Initial Run tab and select the Use Cloud-Init/Sysprep check box.
- Enter a host name in the VM Hostname text field.
- Select the Configure Time Zone check box and select a time zone from the Time Zone drop-down list.
- Expand the Authentication section and select the Use already configured password check box to user the existing credentials, or clear that check box and enter a root password in the Password and Verify Password text fields to specify a new root password.
- Enter any SSH keys to be added to the authorized hosts file on the virtual machine in the SSH Authorized Keys text area.
- Select the Regenerate SSH Keys check box to regenerate SSH keys for the virtual machine.
- Expand the Networks section and enter any DNS servers in the DNS Servers text field.
- Enter any DNS search domains in the DNS Search Domains text field.
- Select the Network check box and use the and buttons to add or remove network interfaces to or from the virtual machine.
- Expand the Custom Script section and enter any custom scripts in the Custom Script text area.
- Click .
- Click and enter the fields as necessary.
- Click .
7.8.4. Using Cloud-Init to Initialize a Virtual Machine
Procedure 7.14. Using Cloud-Init to Initialize a Virtual Machine
- Click the Virtual Machines tab and select a virtual machine.
- Click .
- Expand the Initial Run section and select the Cloud-Init check box.
- Enter a host name in the VM Hostname text field.
- Select the Configure Time Zone check box and select a time zone from the Time Zone drop-down menu.
- Select the Use already configured password check box to use the existing credentials, or clear that check box and enter a root password in the Password and Verify Password text fields to specify a new root password.
- Enter any SSH keys to be added to the authorized hosts file on the virtual machine in the SSH Authorized Keys text area.
- Select the Regenerate SSH Keys check box to regenerate SSH keys for the virtual machine.
- Enter any DNS servers in the DNS Servers text field.
- Enter any DNS search domains in the DNS Search Domains text field.
- Select the Network check box and use the + and - buttons to add or remove network interfaces to or from the virtual machine.
- Enter a custom script in the Custom Script text area. Make sure the values specified in the script are appropriate. Otherwise, the action will fail.
- Click .
Note
7.9. Using Sysprep to Automate the Configuration of Virtual Machines
/usr/share/ovirt-engine/conf/sysprep/ directory. You can also create a custom Sysprep file and reference it from the the osinfo file in the /etc/ovirt-engine/osinfo.conf.d/ directory. These files act as templates for Sysprep. The fields in these files can be copied and edited as required. This definition will override any values entered into the Initial Run fields of the Edit Virtual Machine window./etc/ovirt-engine/osinfo.conf.d/, have a filename that puts it after /etc/ovirt-engine/osinfo.conf.d/00-defaults.properties, and ends in .properties. For example, /etc/ovirt-engine/osinfo.conf.d/10-productkeys.properties. The last file will have precedence and override any other previous file./etc/ovirt-engine/osinfo.conf.d/00-defaults.properties into the override file, and input your values in the productKey.value and sysprepPath.value fields.Example 7.2. Windows 7 Default Configuration Values
# Windows7(11, OsType.Windows, false),false
os.windows_7.id.value = 11
os.windows_7.name.value = Windows 7
os.windows_7.derivedFrom.value = windows_xp
os.windows_7.sysprepPath.value = ${ENGINE_USR}/conf/sysprep/sysprep.w7
os.windows_7.productKey.value =
os.windows_7.devices.audio.value = ich6
os.windows_7.devices.diskInterfaces.value.3.3 = IDE, VirtIO_SCSI, VirtIO
os.windows_7.devices.diskInterfaces.value.3.4 = IDE, VirtIO_SCSI, VirtIO
os.windows_7.devices.diskInterfaces.value.3.5 = IDE, VirtIO_SCSI, VirtIO
os.windows_7.isTimezoneTypeInteger.value = false
7.9.1. Configuring Sysprep on a Template
/usr/share/ovirt-engine/conf/sysprep/ directory. For example, "<Domain><![CDATA[$JoinDomain$]]></Domain>" can be used to indicate the domain to join.Important
Prerequisites
- The Windows virtual machine parameters have been correctly defined.
- If not, click Edit the Virtual Machines tab and enter the required information in the Operating System and Cluster fields.
- The correct product key has been defined in an override file on the Manager.
Procedure 7.15. Using Sysprep to Prepare a Template
- Build the Windows virtual machine with the required patches and layered software.
- Seal the Windows virtual machine. See Section 7.1, “Sealing Virtual Machines in Preparation for Deployment as Templates”
- Create a template based on the Windows virtual machine. See Section 7.2, “Creating a Template”
- Update the Sysprep file with a text editor if additional changes are required.
7.9.2. Using Sysprep to Initialize a Virtual Machine
Procedure 7.16. Using Sysprep to Initialize a Virtual Machine
- Create a new Windows virtual machine based on a template of the required Windows virtual machine. See Section 7.10, “Creating a Virtual Machine Based on a Template”
- Click the Virtual Machines tab and select the virtual machine.
- Click .
- Expand the Boot Options section, select the Attach Floppy check box, and select the [sysprep] option.
- Select the Attach CD check box and select the required Windows ISO from the drop-down list.
- Move the CD-ROM to the top of the Boot Sequence field.
- Configure any further options as required. See Section A.5, “Explanation of Settings in the Run Once Window” for more details.
- Click .
7.10. Creating a Virtual Machine Based on a Template
Note
Procedure 7.17. Creating a Virtual Machine Based on a Template
- Click the Virtual Machines tab.
- Click .
- Select the Cluster on which the virtual machine will run.
- Select a template from the Based on Template list.
- Enter a Name, Description, and any Comments, and accept the default values inherited from the template in the rest of the fields. You can change them if needed.
- Click the Resource Allocation tab.
- Select the Thin radio button in the Storage Allocation area.
- Use the Target drop-down list to select the storage domain on which the virtual machine's virtual disk will be stored.
- Click .
7.11. Creating a Cloned Virtual Machine Based on a Template
Note
Procedure 7.18. Cloning a Virtual Machine Based on a Template
- Click the Virtual Machines tab.
- Click .
- Select the Cluster on which the virtual machine will run.
- Select a template from the Based on Template drop-down menu.
- Enter a Name, Description and any Comments. You can accept the default values inherited from the template in the rest of the fields, or change them if required.
- Click the Resource Allocation tab.
- Select the Clone radio button in the Storage Allocation area.
- Select the disk format from the Format drop-down list. This affects the speed of the clone operation and the amount of disk space the new virtual machine initially requires.
- Selecting QCOW2 results in a faster clone operation and provides optimized usage of storage capacity. Disk space is allocated only as it is required. This is the default selection.
- Selecting Raw results in a slower clone operation and provides optimized virtual machine read and write operations. All disk space requested in the template is allocated at the time of the clone operation.
- Use the Target drop-down menu to select the storage domain on which the virtual machine's virtual disk will be stored.
- Click .
Note
Appendix A. Reference: Settings in Administration Portal and User Portal Windows
A.1. Explanation of Settings in the New Virtual Machine and Edit Virtual Machine Windows
A.1.1. Virtual Machine General Settings Explained
Table A.1. Virtual Machine: General Settings
Field Name | Description |
|---|---|
Cluster | The name of the host cluster to which the virtual machine is attached. Virtual machines are hosted on any physical machine in that cluster in accordance with policy rules. |
Template | The template on which the virtual machine is based. This field is set to Blank by default, which allows you to create a virtual machine on which an operating system has not yet been installed. Templates are displayed as Name | Sub-version name (Sub-version number). Each new version is displayed with a number in brackets that indicates the relative order of the version, with a higher number indicating a more recent version.The version name is displayed as base version if it is the root template of the template version chain.When the virtual machine is stateless, there is an option to select the latest version of the template. This option means that anytime a new version of this template is created, the virtual machine is automatically recreated on restart based on the latest template. |
Operating System | The operating system. Valid values include a range of Red Hat Enterprise Linux and Windows variants. |
Instance Type | The instance type on which the virtual machine's hardware configuration can be based. This field is set to Custom by default, which means the virtual machine is not connected to an instance type. The other options available from this drop down menu are Large, Medium, Small, Tiny, XLarge, and any custom instance types that the Administrator has created. Other settings that have a chain link icon next to them are pre-filled by the selected instance type. If one of these values is changed, the virtual machine will be detached from the instance type and the chain icon will appear broken. However, if the changed setting is restored to its original value, the virtual machine will be reattached to the instance type and the links in the chain icon will rejoin. |
Optimized for | The type of system for which the virtual machine is to be optimized. There are two options: Server, and Desktop; by default, the field is set to Server. Virtual machines optimized to act as servers have no sound card, use a cloned disk image, and are not stateless. In contrast, virtual machines optimized to act as desktop machines do have a sound card, use an image (thin allocation), and are stateless. |
Name | The name of the virtual machine. The name must be a unique name within the data center and must not contain any spaces, and must contain at least one character from A-Z or 0-9. The maximum length of a virtual machine name is 255 characters. The name can be re-used in different data centers in the environment. |
VM ID | The virtual machine ID. The virtual machine's creator can set a custom ID for that virtual machine. If no ID is specified during creation a UUID will be automatically assigned. For both custom and automatically-generated IDs, changes are not possible after virtual machine creation. |
Description | A meaningful description of the new virtual machine. |
Comment | A field for adding plain text human-readable comments regarding the virtual machine. |
Stateless | Select this check box to run the virtual machine in stateless mode. This mode is used primarily for desktop virtual machines. Running a stateless desktop or server creates a new COW layer on the VM hard disk image where new and changed data is stored. Shutting down the stateless VM deletes the new COW layer, which returns the VM to its original state. Stateless virtual machines are useful when creating machines that need to be used for a short time, or by temporary staff. |
Start in Pause Mode | Select this check box to always start the virtual machine in pause mode. This option is suitable for virtual machines which require a long time to establish a SPICE connection; for example, virtual machines in remote locations. |
Delete Protection | Select this check box to make it impossible to delete the virtual machine. It is only possible to delete the virtual machine if this check box is not selected. |
Instance Images | Click to attach a floating disk to the virtual machine, or click to add a new virtual disk. Use the plus and minus buttons to add or remove additional virtual disks. Click to reopen the Attach Virtual Disks or New Virtual Disk window. This button appears after a virtual disk has been attached or created. |
Instantiate VM network interfaces by picking a vNIC profile. | Add a network interface to the virtual machine by selecting a vNIC profile from the nic1 drop-down list. Use the plus and minus buttons to add or remove additional network interfaces. |
A.1.2. Virtual Machine System Settings Explained
Table A.2. Virtual Machine: System Settings
Field Name | Description |
|---|---|
Memory Size | The amount of memory assigned to the virtual machine. When allocating memory, consider the processing and storage needs of the applications that are intended to run on the virtual machine. Maximum guest memory is constrained by the selected guest architecture and the cluster compatibility level. |
Total Virtual CPUs | The processing power allocated to the virtual machine as CPU Cores. Do not assign more cores to a virtual machine than are present on the physical host. |
Virtual Sockets | The number of CPU sockets for the virtual machine. Do not assign more sockets to a virtual machine than are present on the physical host. |
Cores per Virtual Socket | The number of cores assigned to each virtual socket. |
Threads per Core | The number of threads assigned to each core. Increasing the value enables simultaneous multi-threading (SMT). IBM POWER8 supports up to 8 threads per core. For x86 (Intel and AMD) CPU types, the recommended value is 1. |
Custom Emulated Machine | This option allows you to specify the machine type. If changed, the virtual machine will only run on hosts that support this machine type. Defaults to the cluster's default machine type. |
Custom CPU Type | This option allows you to specify a CPU type. If changed, the virtual machine will only run on hosts that support this CPU type. Defaults to the cluster's default CPU type. |
Custom Compatibility Version | The compatibility version determines which features are supported by the cluster, as well as, the values of some properties and the emulated machine type. By default, the virtual machine is configured to run in the same compatibility mode as the cluster as the default is inherited from the cluster. In some situations the default compatibility mode needs to be changed. An example of this is if the cluster has been updated to a newer compatibility version but the virtual machines have not been restarted. These virtual machines can be set to use a custom compatibility mode that is older than that of the cluster. See Changing the Cluster Compatibility Version in the Administration Guide for more information. |
Hardware Clock Time Offset | This option sets the time zone offset of the guest hardware clock. For Windows, this should correspond to the time zone set in the guest. Most default Linux installations expect the hardware clock to be GMT+00:00. |
Provide custom serial number policy | This check box allows you to specify a serial number for the virtual machine. Select either:
|
A.1.3. Virtual Machine Initial Run Settings Explained
Table A.3. Virtual Machine: Initial Run Settings
Field Name | Operating System | Description |
|---|---|---|
Use Cloud-Init/Sysprep | Linux, Windows | This check box toggles whether Cloud-Init or Sysprep will be used to initialize the virtual machine. |
VM Hostname | Linux, Windows | The host name of the virtual machine. |
| Domain | Windows | The Active Directory domain to which the virtual machine belongs. |
| Organization Name | Windows | The name of the organization to which the virtual machine belongs. This option corresponds to the text field for setting the organization name displayed when a machine running Windows is started for the first time. |
| Active Directory OU | Windows | The organizational unit in the Active Directory domain to which the virtual machine belongs. |
Configure Time Zone | Linux, Windows | The time zone for the virtual machine. Select this check box and select a time zone from the Time Zone list. |
| Admin Password | Windows | The administrative user password for the virtual machine. Click the disclosure arrow to display the settings for this option.
|
| Authentication | Linux | The authentication details for the virtual machine. Click the disclosure arrow to display the settings for this option.
|
| Custom Locale | Windows | Custom locale options for the virtual machine. Locales must be in a format such as en-US. Click the disclosure arrow to display the settings for this option.
|
Networks | Linux | Network-related settings for the virtual machine. Click the disclosure arrow to display the settings for this option.
|
Custom Script | Linux | Custom scripts that will be run on the virtual machine when it starts. The scripts entered in this field are custom YAML sections that are added to those produced by the Manager, and allow you to automate tasks such as creating users and files, configuring yum repositories and running commands. For more information on the format of scripts that can be entered in this field, see the Custom Script documentation. |
| Sysprep | Windows | A custom Sysprep definition. The definition must be in the format of a complete unattended installation answer file. You can copy and paste the default answer files in the /usr/share/ovirt-engine/conf/sysprep/ directory on the machine on which the Red Hat Virtualization Manager is installed and alter the fields as required. See Chapter 7, Templates for more information. |
A.1.4. Virtual Machine Console Settings Explained
Table A.4. Virtual Machine: Console Settings
Field Name | Description |
|---|---|
Headless Mode | Enables and disables the graphical console for the virtual machine. If Headless Mode is set, the virtual machine will run after next restart without a graphical console and display device. |
Video Type | Defines the graphics device. QXL is the default and supports both graphic protocols. VGA and CIRRUS support only the VNC protocol. |
Graphics protocol | Defines which display protocol to use. SPICE is the default protocol. VNC is an alternative option. To allow both protocols select SPICE + VNC. |
VNC Keyboard Layout | Defines the keyboard layout for the virtual machine. This option is only available when using the VNC protocol. |
USB Support | Defines SPICE USB redirection. This option is only available for virtual machines using the SPICE protocol. Select either:
|
Console Disconnect Action | Defines what happens when the console is disconnected. This is only relevant with SPICE and VNC console connections. This setting can be changed while the virtual machine is running but will not take effect until a new console connection is established. Select either:
|
Monitors | The number of monitors for the virtual machine. This option is only available for virtual desktops using the SPICE display protocol. You can choose 1, 2 or 4. Note that multiple monitors are not supported for Windows 8 and Windows Server 2012 virtual machines. |
Smartcard Enabled | Smart cards are an external hardware security feature, most commonly seen in credit cards, but also used by many businesses as authentication tokens. Smart cards can be used to protect Red Hat Virtualization virtual machines. Tick or untick the check box to activate and deactivate Smart card authentication for individual virtual machines. |
Single Sign On method | Enabling Single Sign On allows users to sign into the guest operating system when connecting to a virtual machine from the User Portal using the Guest Agent.
|
Disable strict user checking | Click the Advanced Parameters arrow and select the check box to use this option. With this option selected, the virtual machine does not need to be rebooted when a different user connects to it. By default, strict checking is enabled so that only one user can connect to the console of a virtual machine. No other user is able to open a console to the same virtual machine until it has been rebooted. The exception is that a SuperUser can connect at any time and replace a existing connection. When a SuperUser has connected, no normal user can connect again until the virtual machine is rebooted.Disable strict checking with caution, because you can expose the previous user's session to the new user. |
Soundcard Enabled | A sound card device is not necessary for all virtual machine use cases. If it is for yours, enable a sound card here. |
Enable SPICE file transfer | Defines whether a user is able to drag and drop files from an external host into the virtual machine's SPICE console. This option is only available for virtual machines using the SPICE protocol. This check box is selected by default. |
Enable SPICE clipboard copy and paste | Defines whether a user is able to copy and paste content from an external host into the virtual machine's SPICE console. This option is only available for virtual machines using the SPICE protocol. This check box is selected by default. |
Enable VirtIO serial console | The VirtIO serial console is emulated through VirtIO channels, using SSH and key pairs, and allows you to access a virtual machine's serial console directly from a client machine's command line, instead of opening a console from the Administration Portal or the User Portal. The serial console requires direct access to the Manager, since the Manager acts as a proxy for the connection, provides information about virtual machine placement, and stores the authentication keys. Select the check box to enable the VirtIO console on the virtual machine. |
A.1.5. Virtual Machine Host Settings Explained
Table A.5. Virtual Machine: Host Settings
Field Name | Sub-element | Description |
|---|---|---|
Start Running On | Defines the preferred host on which the virtual machine is to run. Select either:
| |
Migration Options | Migration mode | Defines options to run and migrate the virtual machine. If the options here are not used, the virtual machine will run or migrate according to its cluster's policy.
|
Use custom migration policy | Defines the migration convergence policy. If the check box is left unselected, the host determines the policy.
| |
Use custom migration downtime | This check box allows you to specify the maximum number of milliseconds the virtual machine can be down during live migration. Configure different maximum downtimes for each virtual machine according to its workload and SLA requirements. Enter 0 to use the VDSM default value. | |
Auto Converge migrations | Only activated with the Legacy migration policy. Allows you to set whether auto-convergence is used during live migration of the virtual machine. Large virtual machines with high workloads can dirty memory more quickly than the transfer rate achieved during live migration, and prevent the migration from converging. Auto-convergence capabilities in QEMU allow you to force convergence of virtual machine migrations. QEMU automatically detects a lack of convergence and triggers a throttle-down of the vCPUs on the virtual machine. Auto-convergence is disabled globally by default.
| |
Enable migration compression | Only activated with the Legacy migration policy. The option allows you to set whether migration compression is used during live migration of the virtual machine. This feature uses Xor Binary Zero Run-Length-Encoding to reduce virtual machine downtime and total live migration time for virtual machines running memory write-intensive workloads or for any application with a sparse memory update pattern. Migration compression is disabled globally by default.
| |
Pass-Through Host CPU | This check box allows virtual machines to take advantage of the features of the physical CPU of the host on which they are situated. This option can only be enabled when Do not allow migration is selected. | |
Configure NUMA | NUMA Node Count | The number of virtual NUMA nodes to assign to the virtual machine. If the Tune Mode is Preferred, this value must be set to 1. |
Tune Mode | The method used to allocate memory.
| |
Opens the NUMA Topology window. This window shows the host's total CPUs, memory, and NUMA nodes, and the virtual machine's virtual NUMA nodes. Pin virtual NUMA nodes to host NUMA nodes by clicking and dragging each vNUMA from the box on the right to a NUMA node on the left. |
A.1.6. Virtual Machine High Availability Settings Explained
Table A.6. Virtual Machine: High Availability Settings
Field Name | Description |
|---|---|
Highly Available | Select this check box if the virtual machine is to be highly available. For example, in cases of host maintenance, all virtual machines are automatically live migrated to another host. If the host crashed and is in a non-responsive state, only virtual machines with high availability are restarted on another host. If the host is manually shut down by the system administrator, the virtual machine is not automatically live migrated to another host. Note that this option is unavailable if the Migration Options setting in the Hosts tab is set to either Allow manual migration only or Do not allow migration. For a virtual machine to be highly available, it must be possible for the Manager to migrate the virtual machine to other available hosts as necessary. |
Priority for Run/Migration queue | Sets the priority level for the virtual machine to be migrated or restarted on another host. |
Watchdog | Allows users to attach a watchdog card to a virtual machine. A watchdog is a timer that is used to automatically detect and recover from failures. Once set, a watchdog timer continually counts down to zero while the system is in operation, and is periodically restarted by the system to prevent it from reaching zero. If the timer reaches zero, it signifies that the system has been unable to reset the timer and is therefore experiencing a failure. Corrective actions are then taken to address the failure. This functionality is especially useful for servers that demand high availability. Watchdog Model: The model of watchdog card to assign to the virtual machine. At current, the only supported model is i6300esb. Watchdog Action: The action to take if the watchdog timer reaches zero. The following actions are available:
|
A.1.7. Virtual Machine Resource Allocation Settings Explained
Table A.7. Virtual Machine: Resource Allocation Settings
Field Name | Sub-element | Description |
|---|---|---|
CPU Allocation | CPU Profile | The CPU profile assigned to the virtual machine. CPU profiles define the maximum amount of processing capability a virtual machine can access on the host on which it runs, expressed as a percent of the total processing capability available to that host. CPU profiles are defined on the cluster level based on quality of service entries created for data centers. |
CPU Shares | Allows users to set the level of CPU resources a virtual machine can demand relative to other virtual machines.
| |
CPU Pinning topology | Enables the virtual machine's virtual CPU (vCPU) to run on a specific physical CPU (pCPU) in a specific host. The syntax of CPU pinning is v#p[_v#p], for example:
In order to pin a virtual machine to a host, you must also select the following on the Host tab:
| |
Memory Allocation | Physical Memory Guaranteed | The amount of physical memory guaranteed for this virtual machine. Should be any number between 0 and the defined memory for this virtual machine. |
Memory Balloon Device Enabled | Enables the memory balloon device for this virtual machine. Enable this setting to allow memory overcommitment in a cluster. Enable this setting for applications that allocate large amounts of memory suddenly but set the guaranteed memory to the same value as the defined memory. Use ballooning for applications and loads that slowly consume memory, occasionally release memory, or stay dormant for long periods of time, such as virtual desktops. See Optimization Settings Explained in the Administration Guide for more information. | |
| IO Threads | IO Threads Enabled | Enables IO threads. Select this check box to improve the speed of disks that have a VirtIO interface by pinning them to a thread separate from the virtual machine's other functions. Improved disk performance increases a virtual machine's overall performance. Disks with VirtIO interfaces are pinned to an IO thread using a round-robin algorithm. |
| Num Of IO Threads | Optionally enter a number value to create multiple IO threads, up to a maximum value of 127. The default value is 1. | |
Storage Allocation | The Storage Allocation option is only available when the virtual machine is created from a template. | |
Thin | Provides optimized usage of storage capacity. Disk space is allocated only as it is required. When selected, the format of the disks will be marked as QCOW2 and you will not be able to change it. | |
Clone | Optimized for the speed of guest read and write operations. All disk space requested in the template is allocated at the time of the clone operation. When selected, you can select either QCOW2 or RAW as the disk format. | |
VirtIO-SCSI Enabled | Allows users to enable or disable the use of VirtIO-SCSI on the virtual machines. | |
Disk Allocation | The Disk Allocation option is only available when the virtual machine is created from a template. | |
Alias | An alias for the virtual disk. By default, the alias is set to the same value as that of the template. | |
Virtual Size | The total amount of disk space that the virtual machine based on the template can use. This value cannot be edited, and is provided for reference only. | |
Format | The format of the virtual disk. The available options are QCOW2 and Raw. If Thin is selected in the Storage Allocation section, then QCOW2 will be automatically selected and cannot be changed. | |
Target | The storage domain on which the virtual disk is stored. By default, the storage domain is set to the same value as that of the template. | |
Disk Profile | The disk profile to assign to the virtual disk. Disk profiles are created based on storage profiles defined in the data centers. |
A.1.8. Virtual Machine Boot Options Settings Explained
Table A.8. Virtual Machine: Boot Options Settings
Field Name | Description |
|---|---|
First Device | After installing a new virtual machine, the new virtual machine must go into Boot mode before powering up. Select the first device that the virtual machine must try to boot:
|
Second Device | Select the second device for the virtual machine to use to boot if the first device is not available. The first device selected in the previous option does not appear in the options. |
Attach CD | If you have selected CD-ROM as a boot device, tick this check box and select a CD-ROM image from the drop-down menu. The images must be available in the ISO domain. |
Enable menu to select boot device | Enables a menu to select the boot device. After the virtual machine starts and connects to the console, but before the virtual machine starts booting, a menu displays that allows you to select the boot device. This option should be enabled before the initial boot to allow you to select the required installation media. |
A.1.9. Virtual Machine Random Generator Settings Explained
Table A.9. Virtual Machine: Random Generator Settings
Field Name | Description |
|---|---|
Random Generator enabled | Selecting this check box enables a paravirtualized Random Number Generator PCI device (virtio-rng). This device allows entropy to be passed from the host to the virtual machine in order to generate a more sophisticated random number. Note that this check box can only be selected if the RNG device exists on the host and is enabled in the host's cluster. |
Period duration (ms) | Specifies the duration of a period in milliseconds. If omitted, the libvirt default of 1000 milliseconds (1 second) is used. If this field is filled, Bytes per period must be filled also. |
Bytes per period | Specifies how many bytes are permitted to be consumed per period. |
Device source: | The source of the random number generator. This is automatically selected depending on the source supported by the host's cluster.
|
A.1.10. Virtual Machine Custom Properties Settings Explained
Table A.10. Virtual Machine: Custom Properties Settings
Field Name | Description | Recommendations and Limitations |
|---|---|---|
sap_agent | Enables SAP monitoring on the virtual machine. Set to true or false. | - |
sndbuf | Enter the size of the buffer for sending the virtual machine's outgoing data over the socket. Default value is 0. | - |
vhost | Disables vhost-net, which is the kernel-based virtio network driver on virtual network interface cards attached to the virtual machine. To disable vhost, the format for this property is: LogicalNetworkName: falseThis will explicitly start the virtual machine without the vhost-net setting on the virtual NIC attached to LogicalNetworkName. | vhost-net provides better performance than virtio-net, and if it is present, it is enabled on all virtual machine NICs by default. Disabling this property makes it easier to isolate and diagnose performance issues, or to debug vhost-net errors; for example, if migration fails for virtual machines on which vhost does not exist. |
viodiskcache | Caching mode for the virtio disk. writethrough writes data to the cache and the disk in parallel, writeback does not copy modifications from the cache to the disk, and none disables caching. See https://access.redhat.com/solutions/2361311 for more information about the limitations of the viodiskcache custom property. | If viodiskcache is enabled, the virtual machine cannot be live migrated. |
Warning
A.1.11. Virtual Machine Icon Settings Explained
Table A.11. Virtual Machine: Icon Settings
Button Name | Description |
|---|---|
Upload | Click this button to select a custom image to use as the virtual machine's icon. The following limitations apply:
|
Use default | Click this button to set the operating system's default image as the virtual machine's icon. |
A.1.12. Virtual Machine Foreman/Satellite Settings Explained
Table A.12. Virtual Machine:Foreman/Satellite Settings
Field Name | Description |
|---|---|
Provider | If the virtual machine is running Red Hat Enterprise Linux and the system is configured to work with a Satellite server, select the name of the Satellite from the list. This enables you to use Satellite's content management feature to display the relevant Errata for this virtual machine. See Section 4.7, “Configuring Red Hat Satellite Errata Management for a Virtual Machine” for more details. |
A.2. Explanation of Settings in the New Network Interface and Edit Network Interface Windows
Table A.13. Network Interface Settings
Field Name | Description |
|---|---|
Name | The name of the network interface. This text field has a 21-character limit and must be a unique name with any combination of uppercase and lowercase letters, numbers, hyphens, and underscores. |
Profile | Logical network that the network interface is placed on. By default, all network interfaces are put on the ovirtmgmt management network. |
Type | The virtual interface the network interface presents to virtual machines. VirtIO is faster but requires VirtIO drivers. Red Hat Enterprise Linux 5 and higher includes VirtIO drivers. Windows does not include VirtIO drivers, but they can be installed from the guest tools ISO or virtual floppy disk. rtl8139 and e1000 device drivers are included in most operating systems. |
Custom MAC address | Choose this option to set a custom MAC address. The Red Hat Virtualization Manager automatically generates a MAC address that is unique to the environment to identify the network interface. Having two devices with the same MAC address online in the same network causes networking conflicts. |
Link State | Whether or not the network interface is connected to the logical network.
|
Card Status | Whether or not the network interface is defined on the virtual machine.
|
A.3. Explanation of Settings in the New Virtual Disk and Edit Virtual Disk Windows
Table A.14. New Virtual Disk and Edit Virtual Disk Settings: Image
Field Name | Description |
|---|---|
Size(GB) | The size of the new virtual disk in GB. |
Alias | The name of the virtual disk, limited to 40 characters. |
Description | A description of the virtual disk. This field is recommended but not mandatory. |
Interface | The virtual interface the disk presents to virtual machines. VirtIO is faster, but requires drivers. Red Hat Enterprise Linux 5 and higher include these drivers. Windows does not include these drivers, but they can be installed from the guest tools ISO or virtual floppy disk. IDE devices do not require special drivers. The interface type can be updated after stopping all virtual machines that the disk is attached to. |
Data Center | The data center in which the virtual disk will be available. |
Storage Domain | The storage domain in which the virtual disk will be stored. The drop-down list shows all storage domains available in the given data center, and also shows the total space and currently available space in the storage domain. |
Allocation Policy | The provisioning policy for the new virtual disk.
|
Disk Profile | The disk profile assigned to the virtual disk. Disk profiles define the maximum amount of throughput and the maximum level of input and output operations for a virtual disk in a storage domain. Disk profiles are defined on the storage domain level based on storage quality of service entries created for data centers. |
Activate Disk(s) | Activate the virtual disk immediately after creation. This option is not available when creating a floating disk. |
Wipe After Delete | Allows you to enable enhanced security for deletion of sensitive material when the virtual disk is deleted. |
Bootable | Allows you to enable the bootable flag on the virtual disk. |
Shareable | Allows you to attach the virtual disk to more than one virtual machine at a time. |
Read-Only | Allows you to set the disk as read-only. The same disk can be attached as read-only to one virtual machine, and as rewritable to another. This option is not available when creating a floating disk. |
Table A.15. New Virtual Disk and Edit Virtual Disk Settings: Direct LUN
Field Name | Description |
|---|---|
Alias | The name of the virtual disk, limited to 40 characters. |
Description | A description of the virtual disk. This field is recommended but not mandatory. By default the last 4 characters of the LUN ID is inserted into the field. The default behavior can be configured by setting the PopulateDirectLUNDiskDescriptionWithLUNId configuration key to the appropriate value using the engine-config command. The configuration key can be set to -1 for the full LUN ID to be used, or 0 for this feature to be ignored. A positive integer populates the description with the corresponding number of characters of the LUN ID. |
Interface | The virtual interface the disk presents to virtual machines. VirtIO is faster, but requires drivers. Red Hat Enterprise Linux 5 and higher include these drivers. Windows does not include these drivers, but they can be installed from the guest tools ISO or virtual floppy disk. IDE devices do not require special drivers. The interface type can be updated after stopping all virtual machines that the disk is attached to. |
Data Center | The data center in which the virtual disk will be available. |
Use Host | The host on which the LUN will be mounted. You can select any host in the data center. |
Storage Type | The type of external LUN to add. You can select from either iSCSI or Fibre Channel. |
Discover Targets | This section can be expanded when you are using iSCSI external LUNs and Targets > LUNs is selected. Address - The host name or IP address of the target server. Port - The port by which to attempt a connection to the target server. The default port is 3260. User Authentication - The iSCSI server requires User Authentication. The User Authentication field is visible when you are using iSCSI external LUNs. CHAP username - The user name of a user with permission to log in to LUNs. This field is accessible when the User Authentication check box is selected. CHAP password - The password of a user with permission to log in to LUNs. This field is accessible when the User Authentication check box is selected. |
Activate Disk(s) | Activate the virtual disk immediately after creation. This option is not available when creating a floating disk. |
Bootable | Allows you to enable the bootable flag on the virtual disk. |
Shareable | Allows you to attach the virtual disk to more than one virtual machine at a time. |
Read-Only | Allows you to set the disk as read-only. The same disk can be attached as read-only to one virtual machine, and as rewritable to another. This option is not available when creating a floating disk. |
Enable SCSI Pass-Through | Available when the Interface is set to VirtIO-SCSI. Selecting this check box enables passthrough of a physical SCSI device to the virtual disk. A VirtIO-SCSI interface with SCSI passthrough enabled automatically includes SCSI discard support. Read-Only is not supported when this check box is selected. When this check box is not selected, the virtual disk uses an emulated SCSI device. Read-Only is supported on emulated VirtIO-SCSI disks. |
Allow Privileged SCSI I/O | Available when the Enable SCSI Pass-Through check box is selected. Selecting this check box enables unfiltered SCSI Generic I/O (SG_IO) access, allowing privileged SG_IO commands on the disk. This is required for persistent reservations. |
Using SCSI Reservation | Available when the Enable SCSI Pass-Through and Allow Privileged SCSI I/O check boxes are selected. Selecting this check box disables migration for any virtual machine using this disk, to prevent virtual machines that are using SCSI reservation from losing access to the disk. |
- Live storage migration of direct LUN hard disk images is not supported.
- Direct LUN disks are not included in virtual machine exports.
- Direct LUN disks are not included in virtual machine snapshots.
Table A.16. New Virtual Disk and Edit Virtual Disk Settings: Cinder
Field Name | Description |
|---|---|
Size(GB) | The size of the new virtual disk in GB. |
Alias | The name of the virtual disk, limited to 40 characters. |
Description | A description of the virtual disk. This field is recommended but not mandatory. |
Interface | The virtual interface the disk presents to virtual machines. VirtIO is faster, but requires drivers. Red Hat Enterprise Linux 5 and higher include these drivers. Windows does not include these drivers, but they can be installed from the guest tools ISO or virtual floppy disk. IDE devices do not require special drivers. The interface type can be updated after stopping all virtual machines that the disk is attached to. |
Data Center | The data center in which the virtual disk will be available. |
Storage Domain | The storage domain in which the virtual disk will be stored. The drop-down list shows all storage domains available in the given data center, and also shows the total space and currently available space in the storage domain. |
Volume Type | The volume type of the virtual disk. The drop-down list shows all available volume types. The volume type will be managed and configured on OpenStack Cinder. |
Activate Disk(s) | Activate the virtual disk immediately after creation. This option is not available when creating a floating disk. |
Bootable | Allows you to enable the bootable flag on the virtual disk. |
Shareable | Allows you to attach the virtual disk to more than one virtual machine at a time. |
Read-Only | Allows you to set the disk as read-only. The same disk can be attached as read-only to one virtual machine, and as rewritable to another. This option is not available when creating a floating disk. |
Important
EXT3, EXT4, or XFS).A.4. Explanation of Settings in the New Template and Edit Template Windows
Table A.17. New Template and Edit Template Settings
Field | Description/Action |
|---|---|
Name | The name of the template. This is the name by which the template is listed in the Templates tab in the Administration Portal and is accessed via the REST API. This text field has a 40-character limit and must be a unique name within the data center with any combination of uppercase and lowercase letters, numbers, hyphens, and underscores. The name can be re-used in different data centers in the environment. |
Description | A description of the template. This field is recommended but not mandatory. |
Comment | A field for adding plain text, human-readable comments regarding the template. |
Cluster | The cluster with which the template is associated. This is the same as the original virtual machines by default. You can select any cluster in the data center. |
| CPU Profile | The CPU profile assigned to the template. CPU profiles define the maximum amount of processing capability a virtual machine can access on the host on which it runs, expressed as a percent of the total processing capability available to that host. CPU profiles are defined on the cluster level based on quality of service entries created for data centers. |
Create as a Template Sub Version | Specifies whether the template is created as a new version of an existing template. Select this check box to access the settings for configuring this option.
|
Disks Allocation | Alias - An alias for the virtual disk used by the template. By default, the alias is set to the same value as that of the source virtual machine. Virtual Size - The total amount of disk space that a virtual machine based on the template can use. This value cannot be edited, and is provided for reference only. This value corresponds with the size, in GB, that was specified when the disk was created or edited. Format - The format of the virtual disk used by the template. The available options are QCOW2 and Raw. By default, the format is set to Raw. Target - The storage domain on which the virtual disk used by the template is stored. By default, the storage domain is set to the same value as that of the source virtual machine. You can select any storage domain in the cluster. Disk Profile - The disk profile to assign to the virtual disk used by the template. Disk profiles are created based on storage profiles defined in the data centers. |
Allow all users to access this Template | Specifies whether a template is public or private. A public template can be accessed by all users, whereas a private template can only be accessed by users with the TemplateAdmin or SuperUser roles. |
Copy VM permissions | Copies explicit permissions that have been set on the source virtual machine to the template. |
A.5. Explanation of Settings in the Run Once Window
Table A.18. Boot Options Section
Field Name | Description |
|---|---|
Attach Floppy | Attaches a diskette image to the virtual machine. Use this option to install Windows drivers. The diskette image must reside in the ISO domain. |
Attach CD | Attaches an ISO image to the virtual machine. Use this option to install the virtual machine's operating system and applications. The CD image must reside in the ISO domain. |
Boot Sequence | Determines the order in which the boot devices are used to boot the virtual machine. Select either Hard Disk, CD-ROM or Network, and use and to move the option up or down in the list. |
Run Stateless | Deletes all changes to the virtual machine upon shutdown. This option is only available if a virtual disk is attached to the virtual machine. |
Start in Pause Mode | Starts then pauses the virtual machine to enable connection to the console, suitable for virtual machines in remote locations. |
Table A.19. Linux Boot Options Section
Field Name | Description |
|---|---|
kernel path | A fully qualified path to a kernel image to boot the virtual machine. The kernel image must be stored on either the ISO domain (path name in the format of iso://path-to-image) or on the host's local storage domain (path name in the format of /data/images). |
initrd path | A fully qualified path to a ramdisk image to be used with the previously specified kernel. The ramdisk image must be stored on the ISO domain (path name in the format of iso://path-to-image) or on the host's local storage domain (path name in the format of /data/images). |
kernel parameters | Kernel command line parameter strings to be used with the defined kernel on boot. |
[sysprep] floppy by selecting the Attach Floppy check box in the Boot Options tab and selecting the floppy from the list.Table A.20. Initial Run Section (Linux-based Virtual Machines)
Field Name | Description |
|---|---|
VM Hostname | The host name of the virtual machine. |
Configure Time Zone | The time zone for the virtual machine. Select this check box and select a time zone from the Time Zone list. |
Authentication | The authentication details for the virtual machine. Click the disclosure arrow to display the settings for this option. |
| Authentication > User Name | Creates a new user account on the virtual machine. If this field is not filled in, the default user is root. |
Authentication > Use already configured password | This check box is automatically selected after you specify an initial root password. You must clear this check box to enable the Password and Verify Password fields and specify a new password. |
Authentication > Password | The root password for the virtual machine. Enter the password in this text field and the Verify Password text field to verify the password. |
Authentication > SSH Authorized Keys | SSH keys to be added to the authorized keys file of the virtual machine. |
Authentication > Regenerate SSH Keys | Regenerates SSH keys for the virtual machine. |
Networks | Network-related settings for the virtual machine. Click the disclosure arrow to display the settings for this option. |
Networks > DNS Servers | The DNS servers to be used by the virtual machine. |
Networks > DNS Search Domains | The DNS search domains to be used by the virtual machine. |
Networks > Network | Configures network interfaces for the virtual machine. Select this check box and click + or - to add or remove network interfaces to or from the virtual machine. When you click +, a set of fields becomes visible that can specify whether to use DHCP, and configure an IP address, netmask, and gateway, and specify whether the network interface will start on boot. |
Custom Script | Custom scripts that will be run on the virtual machine when it starts. The scripts entered in this field are custom YAML sections that are added to those produced by the Manager, and allow you to automate tasks such as creating users and files, configuring yum repositories and running commands. For more information on the format of scripts that can be entered in this field, see the Custom Script documentation. |
Table A.21. Initial Run Section (Windows-based Virtual Machines)
Field Name | Description |
|---|---|
VM Hostname | The host name of the virtual machine. |
Domain | The Active Directory domain to which the virtual machine belongs. |
Organization Name | The name of the organization to which the virtual machine belongs. This option corresponds to the text field for setting the organization name displayed when a machine running Windows is started for the first time. |
Active Directory OU | The organizational unit in the Active Directory domain to which the virtual machine belongs. The distinguished name must be provided. For example CN=Users,DC=lab,DC=local |
Configure Time Zone | The time zone for the virtual machine. Select this check box and select a time zone from the Time Zone list. |
Admin Password | The administrative user password for the virtual machine. Click the disclosure arrow to display the settings for this option. |
Admin Password > Use already configured password | This check box is automatically selected after you specify an initial administrative user password. You must clear this check box to enable the Admin Password and Verify Admin Password fields and specify a new password. |
Admin Password > Admin Password | The administrative user password for the virtual machine. Enter the password in this text field and the Verify Admin Password text field to verify the password. |
Custom Locale | Locales must be in a format such as en-US. Click the disclosure arrow to display the settings for this option. |
Custom Locale > Input Locale | The locale for user input. |
Custom Locale > UI Language | The language used for user interface elements such as buttons and menus. |
Custom Locale > System Locale | The locale for the overall system. |
Custom Locale > User Locale | The locale for users. |
Sysprep | A custom Sysprep definition. The definition must be in the format of a complete unattended installation answer file. You can copy and paste the default answer files in the /usr/share/ovirt-engine/conf/sysprep/ directory on the machine on which the Red Hat Virtualization Manager is installed and alter the fields as required. The definition will overwrite any values entered in the Initial Run fields. See Chapter 7, Templates for more information. |
Domain | The Active Directory domain to which the virtual machine belongs. If left blank, the value of the previous Domain field is used. |
Alternate Credentials | Selecting this check box allows you to set a User Name and Password as alternative credentials. |
Table A.22. System Section
Field Name | Description |
|---|---|
Custom Emulated Machine | This option allows you to specify the machine type. If changed, the virtual machine will only run on hosts that support this machine type. Defaults to the cluster's default machine type. |
Custom CPU Type | This option allows you to specify a CPU type. If changed, the virtual machine will only run on hosts that support this CPU type. Defaults to the cluster's default CPU type. |
Table A.23. Host Section
Field Name | Description |
|---|---|
Any host in cluster | Allocates the virtual machine to any available host. |
Specific | Specifies a user-defined host for the virtual machine. |
Table A.24. Console Section
Field Name | Description |
|---|---|
VNC | Requires a VNC client to connect to a virtual machine using VNC. Optionally, specify VNC Keyboard Layout from the drop-down list. |
SPICE | Recommended protocol for Linux and Windows virtual machines. Using SPICE protocol without QXL drivers is supported for Windows 8 and Server 2012 virtual machines; however, support for multiple monitors and graphics acceleration is not available for this configuration. |
Table A.25. Custom Properties Section
Field Name | Description |
|---|---|
sap_agent | Enables SAP monitoring on the virtual machine. Set to true or false. |
sndbuf | Enter the size of the buffer for sending the virtual machine's outgoing data over the socket. |
vhost | Enter the name of the virtual host on which this virtual machine should run. The name can contain any combination of letters and numbers. |
viodiskcache | Caching mode for the virtio disk. writethrough writes data to the cache and the disk in parallel, writeback does not copy modifications from the cache to the disk, and none disables caching. See https://access.redhat.com/solutions/2361311 for more information about the limitations of the viodiskcache custom property. |
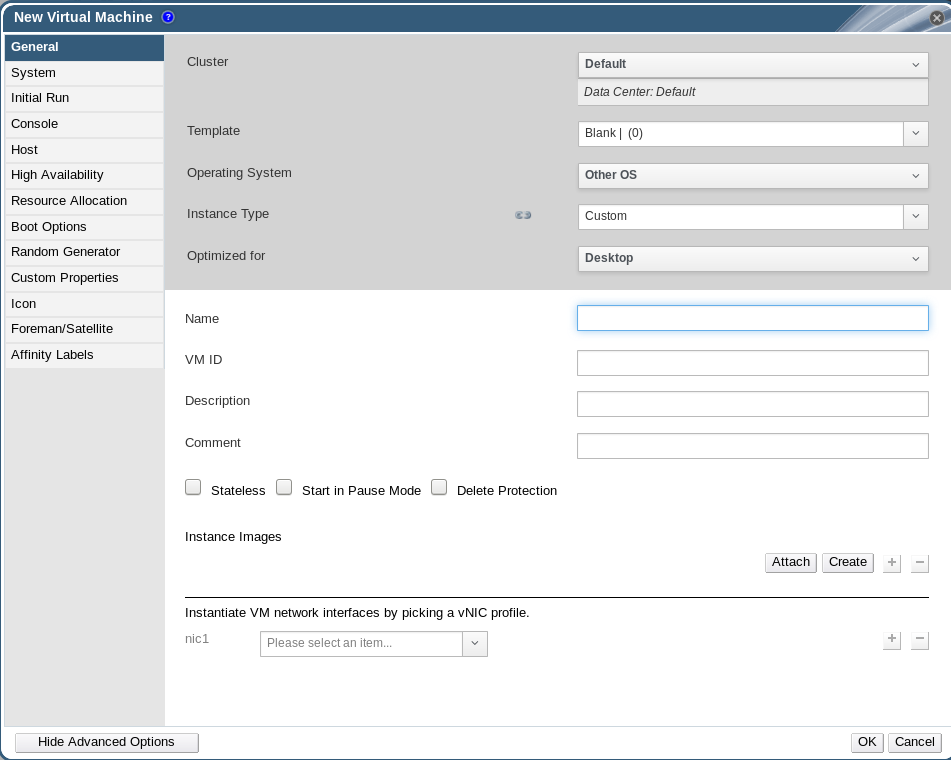

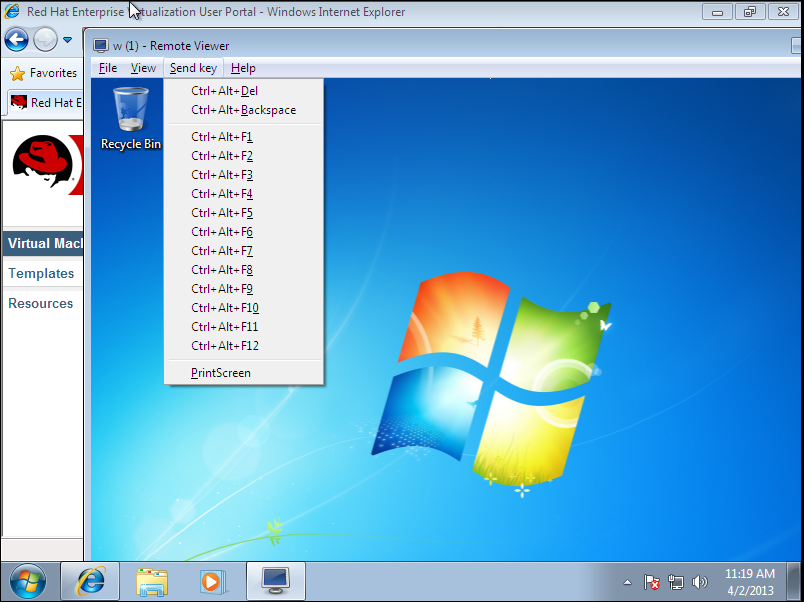
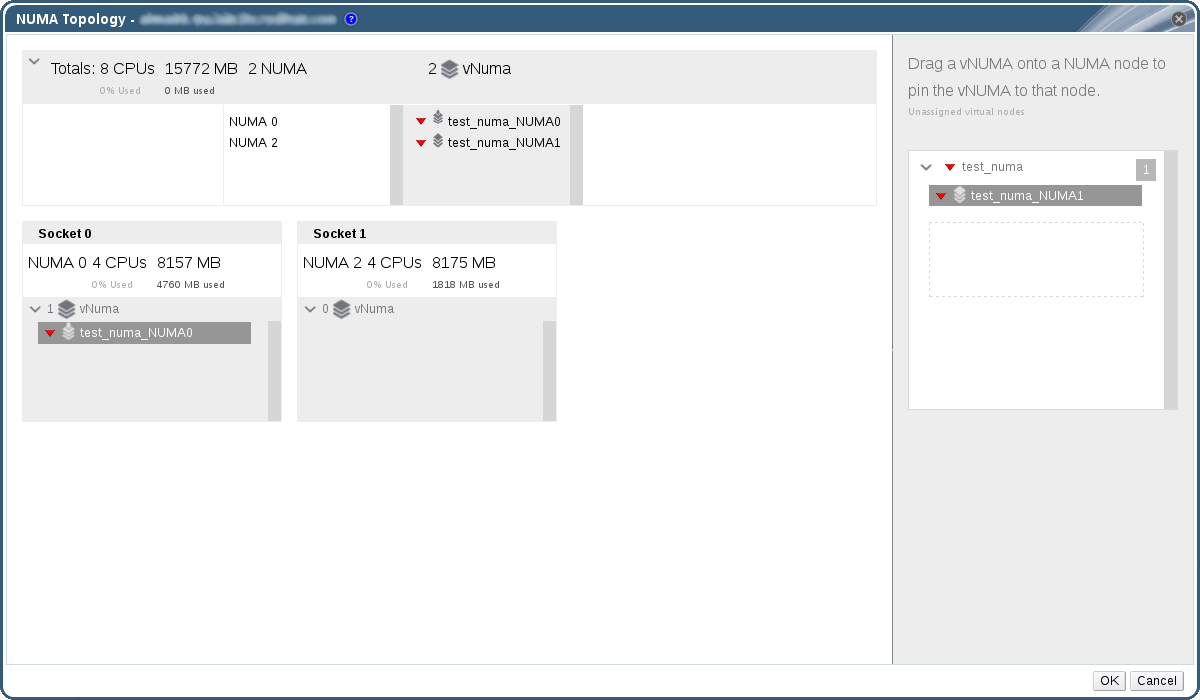



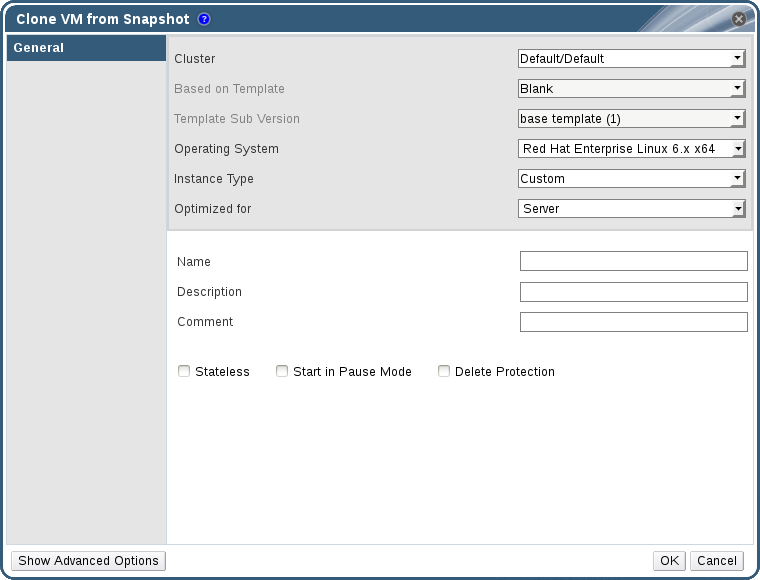
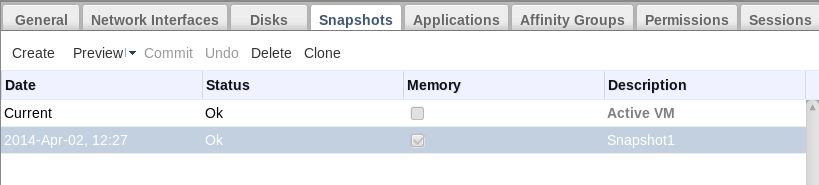
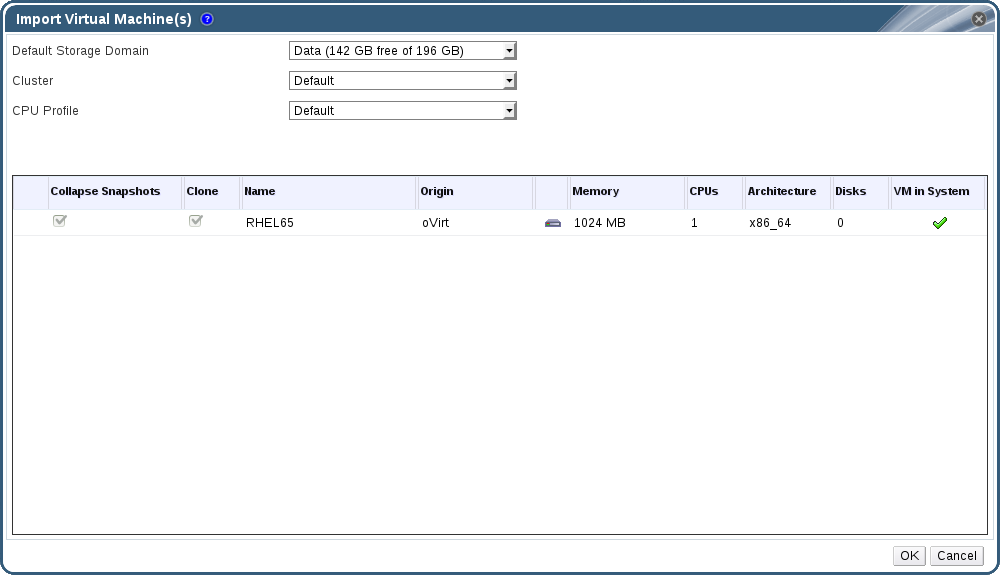
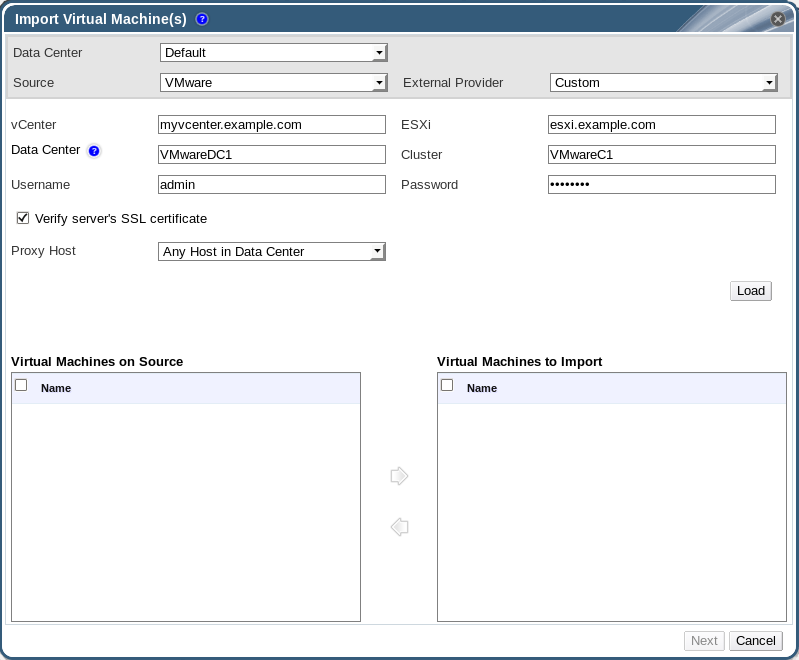
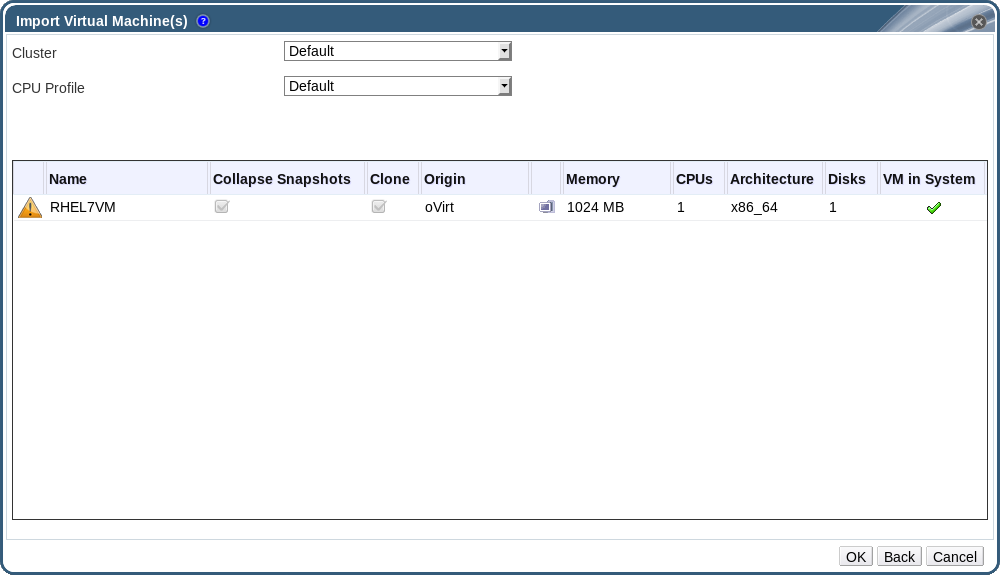

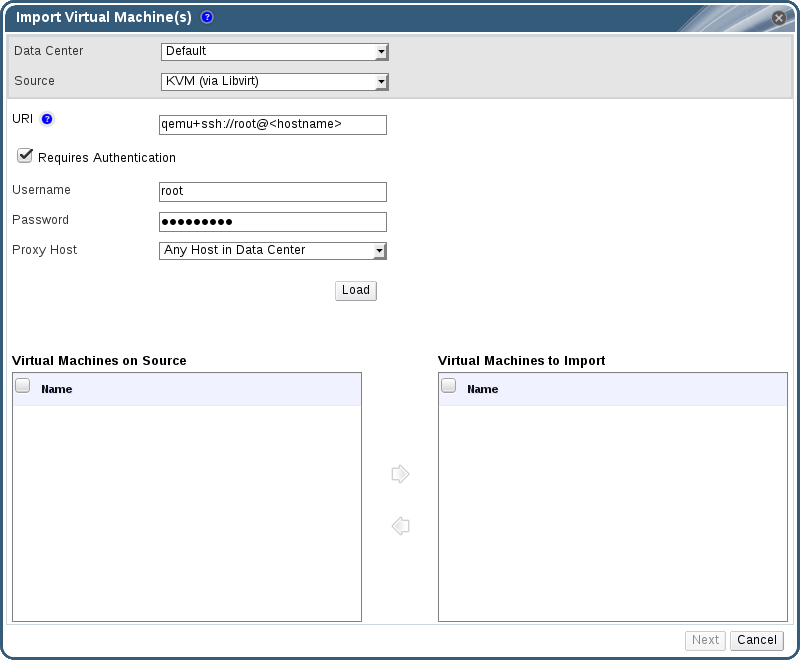
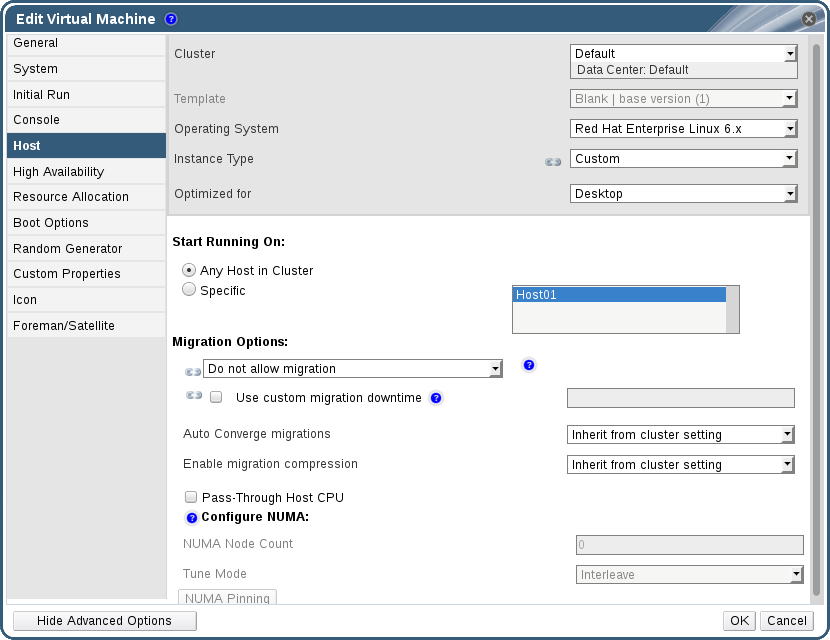

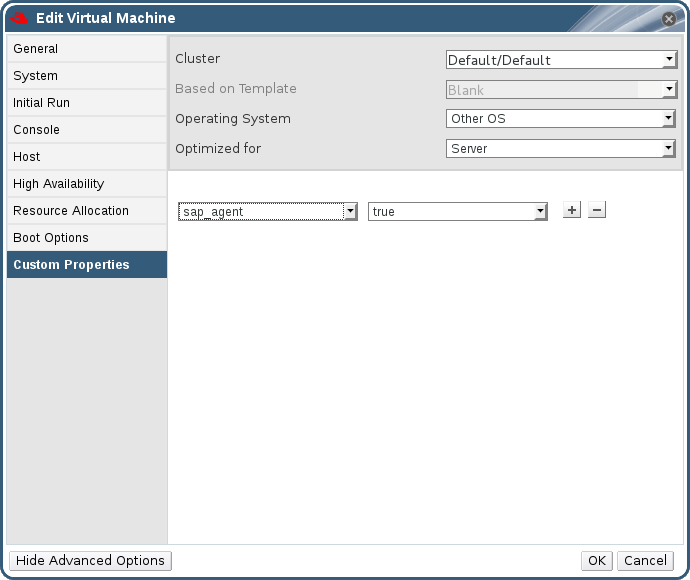
Tidak ada komentar:
Posting Komentar