Setting Up Harbor Registry on Kubernetes Using Helm Chart

Harbor is an open-source container image registry that secures images with role-based access control, scans images for vulnerabilities, and signs images as trusted. Setting up Harbor on Kubernetes using Helm is a streamlined process that allows you to deploy a fully functional container registry quickly and efficiently. This guide walks you through the necessary steps to set up Harbor using a Helm chart.
Prerequisites
Before you start, ensure you have the following prerequisites:
- Kubernetes Cluster: A running Kubernetes cluster (v1.12+).
- Helm: Helm 3 installed on your local machine.
- kubectl: kubectl installed and configured to interact with your Kubernetes cluster.
Step 1: Add the Harbor Helm Repository
First, add the Harbor Helm repository to your Helm client:
helm repo add harbor https://helm.goharbor.io
helm repo updateStep 2: Create a Namespace for Harbor
Create a dedicated namespace for Harbor to keep things organized:
kubectl create namespace harborStep 3: Install Harbor with Helm
You can install Harbor with the default configuration using the following command:
helm install harbor harbor/harbor --namespace harborThis will deploy Harbor with default settings. However, for production environments, you may want to customize the configuration.
Step 4: Customize Harbor Configuration
To customize Harbor’s settings, you need to have SSL certs and a custom configuration created in a values.yaml file. This file allows you to override default settings.
Step 4a: Create SSL Certs
Container registry needs to have TLS certificate signed by known certificate authority. Although self sign certificates can be used when deploying harbor but images push/pull will fail unless you trust CA. Free SSL certs signed by CA can be generated using LetsEncrypt certbot or from this portal. Once you get the certificate and key, rename the cert to tls.crt and key to tls.key and store the certs content as a Secret.
kubectl create secret tls harbor-cert --key tls.key --cert tls.crt -n harborStep 4b: Install Harbor using custom configuration
Here is an example of a basic values.yaml file which uses the above secret create containing ssl cert. Make sure your Kubernetes service provider supports service type Load Balancer.
expose:
# Set how to expose the service. Set the type as "ingress", "clusterIP", "nodePort" or "loadBalancer"
# and fill the information in the corresponding section
type: loadBalancer
tls:
# Enable TLS or not.
# Delete the "ssl-redirect" annotations in "expose.ingress.annotations" when TLS is disabled and "expose.type" is "ingress"
# Note: if the "expose.type" is "ingress" and TLS is disabled,
# the port must be included in the command when pulling/pushing images.
# Refer to https://github.com/goharbor/harbor/issues/5291 for details.
enabled: true
# The source of the tls certificate. Set as "auto", "secret"
# or "none" and fill the information in the corresponding section
# 1) auto: generate the tls certificate automatically
# 2) secret: read the tls certificate from the specified secret.
# The tls certificate can be generated manually or by cert manager
# 3) none: configure no tls certificate for the ingress. If the default
# tls certificate is configured in the ingress controller, choose this option
certSource: secret
auto:
# The common name used to generate the certificate, it's necessary
# when the type isn't "ingress"
commonName: ""
secret:
# The name of secret which contains keys named:
# "tls.crt" - the certificate
# "tls.key" - the private key
secretName: "harbor-cert"
notarySecretName: "harbor-cert"
ingress:
hosts:
core: harbor.mydomain.com
notary: harbor.mydomain.com
# The external URL for Harbor core service. It is used to
# 1) populate the docker/helm commands showed on portal
# 2) populate the token service URL returned to docker client
#
# Format: protocol://domain[:port]. Usually:
# 1) if "expose.type" is "ingress", the "domain" should be
# the value of "expose.ingress.hosts.core"
# 2) if "expose.type" is "clusterIP", the "domain" should be
# the value of "expose.clusterIP.name"
# 3) if "expose.type" is "nodePort", the "domain" should be
# the IP address of k8s node
#
# If Harbor is deployed behind the proxy, set it as the URL of proxy
externalURL: https://harbor.mydomain.com
# The initial password of Harbor admin. Change it from portal after launching Harbor
# or give an existing secret for it
# key in secret is given via (default to HARBOR_ADMIN_PASSWORD)
# existingSecretAdminPassword:
existingSecretAdminPasswordKey: HARBOR_ADMIN_PASSWORD
harborAdminPassword: "Harbor@12345"Step 5: Deploy Harbor with Custom Values
Use your custom values.yaml file to deploy Harbor:
helm install harbor harbor/harbor --namespace harbor -f values.yamlStep 6: Verify the Installation
Check the status of your Harbor deployment:
helm status harbor -n harborEnsure all Harbor components are running:
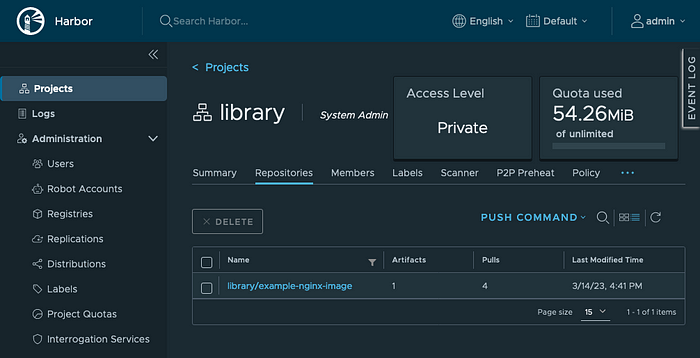
kubectl get pods -n harborStep 7: Access Harbor
If you’ve configured Harbor to use an ingress, you can access it via the URL specified in your values.yaml file (e.g., https://harbor.mydomain.com). Ensure your DNS settings are configured to point to your Kubernetes load balancer IP.
End Note
Above configuration is a very basic configuration. For a production grade setup, make sure that you setup external Database and external Redis setup created and used with Harbor.
Loved this?
So, did you find this article helpful? If you did, please consider buying me a coffee :-)
Tidak ada komentar:
Posting Komentar